Deployment of Microsoft Sentinel SIEM on Azure and SIEM Integration with Artificial Intelligence (ChatGPT)
Microsoft-Sentinel-SIEM-Project
Configure and Deploy Microsoft Sentinel SIEM and integrate with ChatGPT
| Category | SIEM Deployment and AI Integration |
|---|---|
| Tactics | Defense Evasion, Incident Response, Threat Hunting, Automated Response |
| Tools | Microsoft Sentinel, Azure Portal, ChatGPT, Azure Logic Apps |
| Difficulty | Intermediate |
| Official Walkthrough | Microsoft Sentinel Documentation |
Introduction
Microsoft Sentinel is a cloud-native SIEM solution developed by Microsoft Azure. It provides advanced security analytics and threat intelligence to swiftly identify, investigate, and address potential security threats. This tutorial aims to provide instructions on configuring the Microsoft Sentinel SIEM function made available in Azure. Through this tutorial, you will be able to create alert rules for response, link data sources, and use Sentinel to investigate past incidents. The tutorial’s primary goal is to explore Microsoft Sentinel’s features step-by-step and demonstrate how to strengthen its cyber defense.
Prerequisites
Before beginning, ensure you have;
- An Azure Subscription
- Access to the Microsoft Azure Portal
- A basic understanding of security operations
Step 1: Setting Up Microsoft Sentinel
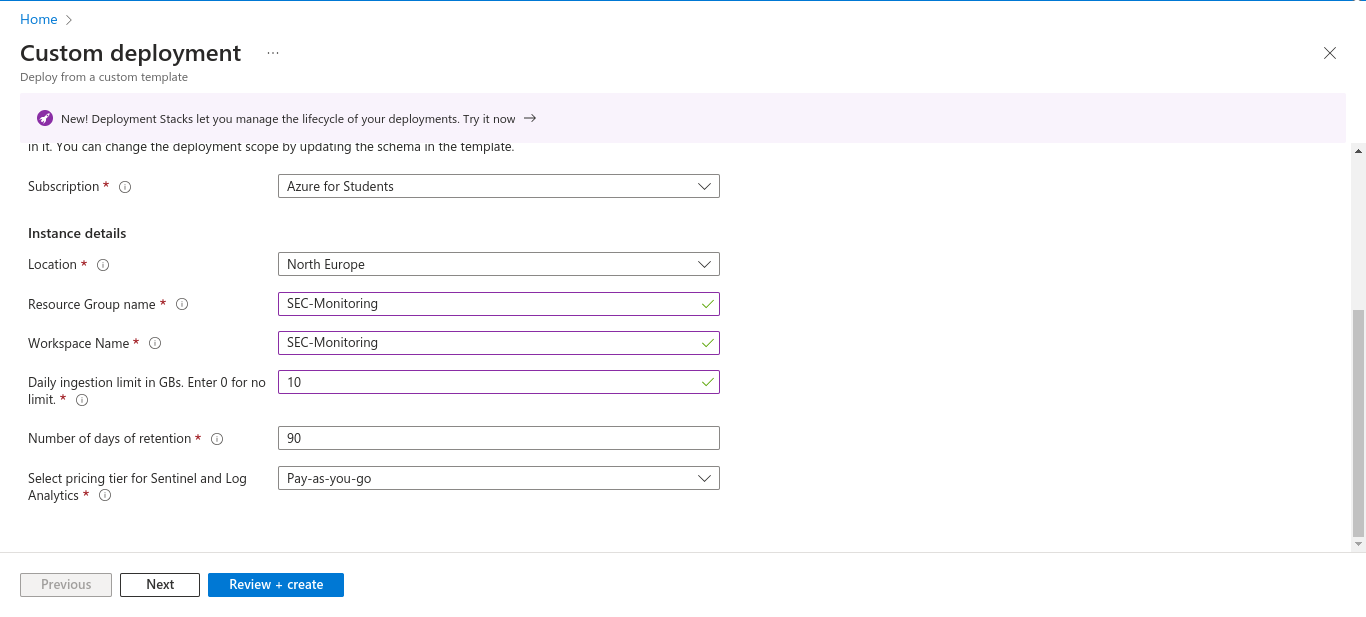
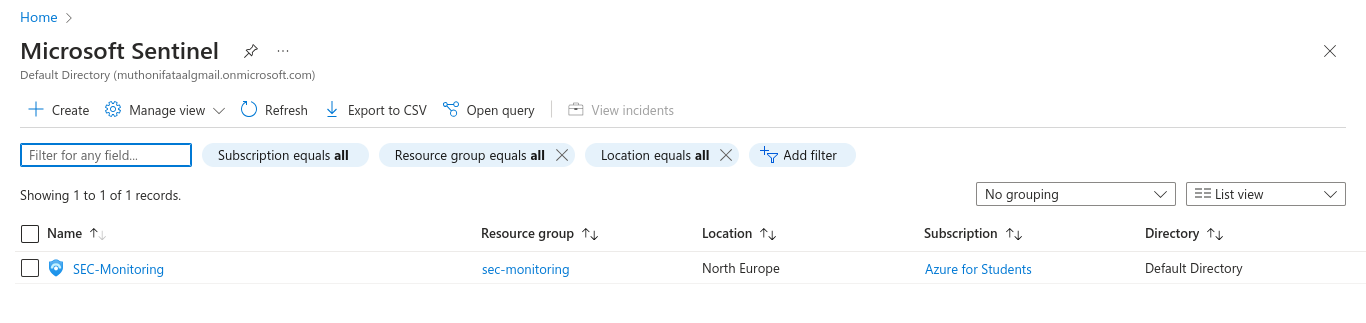
Create Azure Workspace - Select the subscription, resource group, and region.
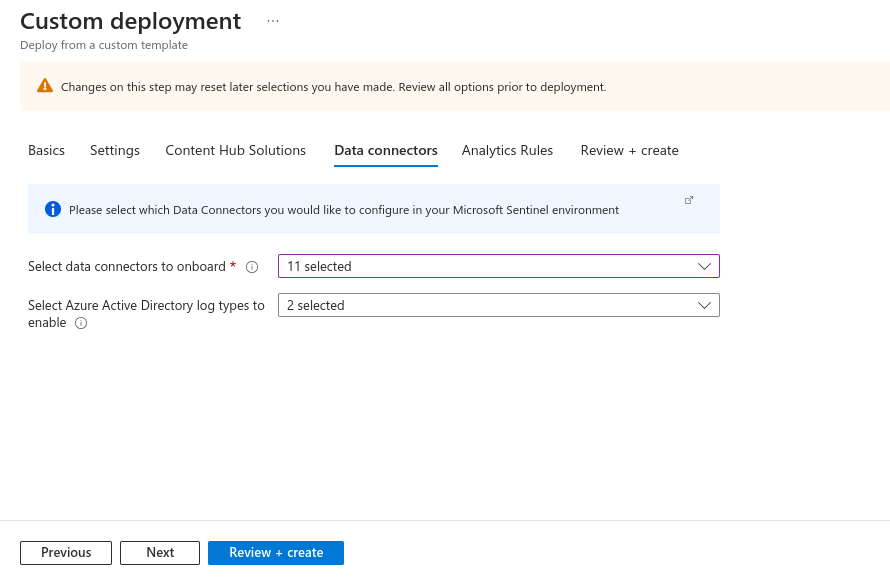
Configure Data Connectors - Set up data connectors for the required data sources, such as Office 365 and Azure Active Directory.
Activate Microsoft Sentinel - Enable Microsoft Sentinel in the Azure Security Center settings.
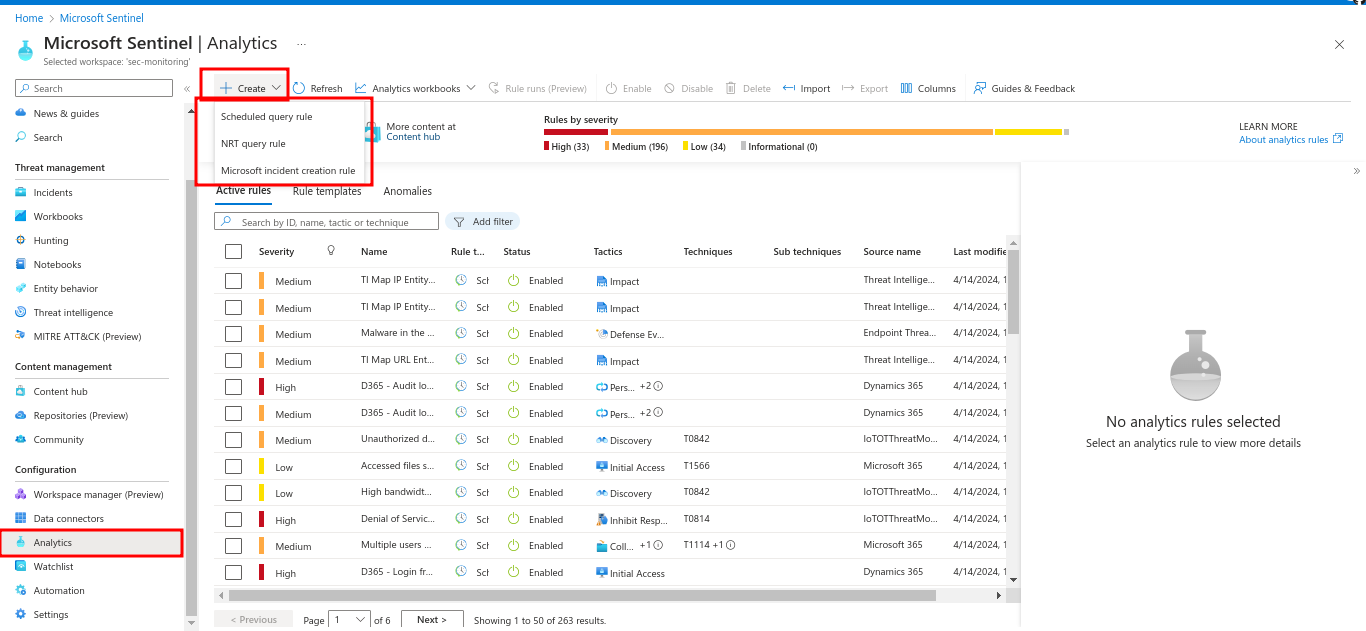
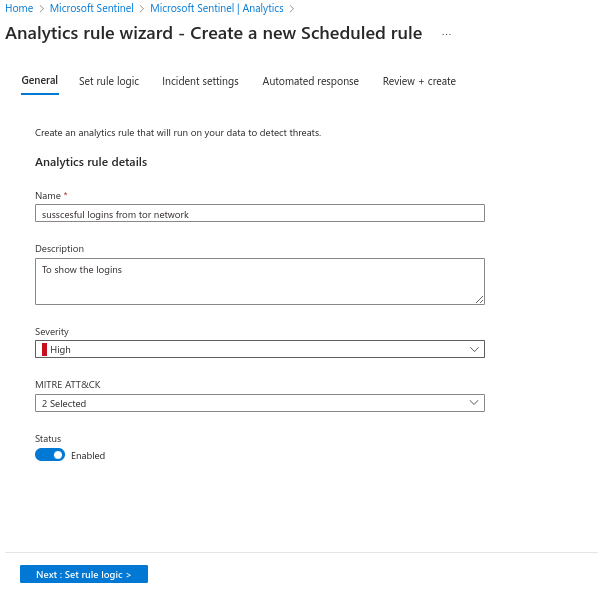
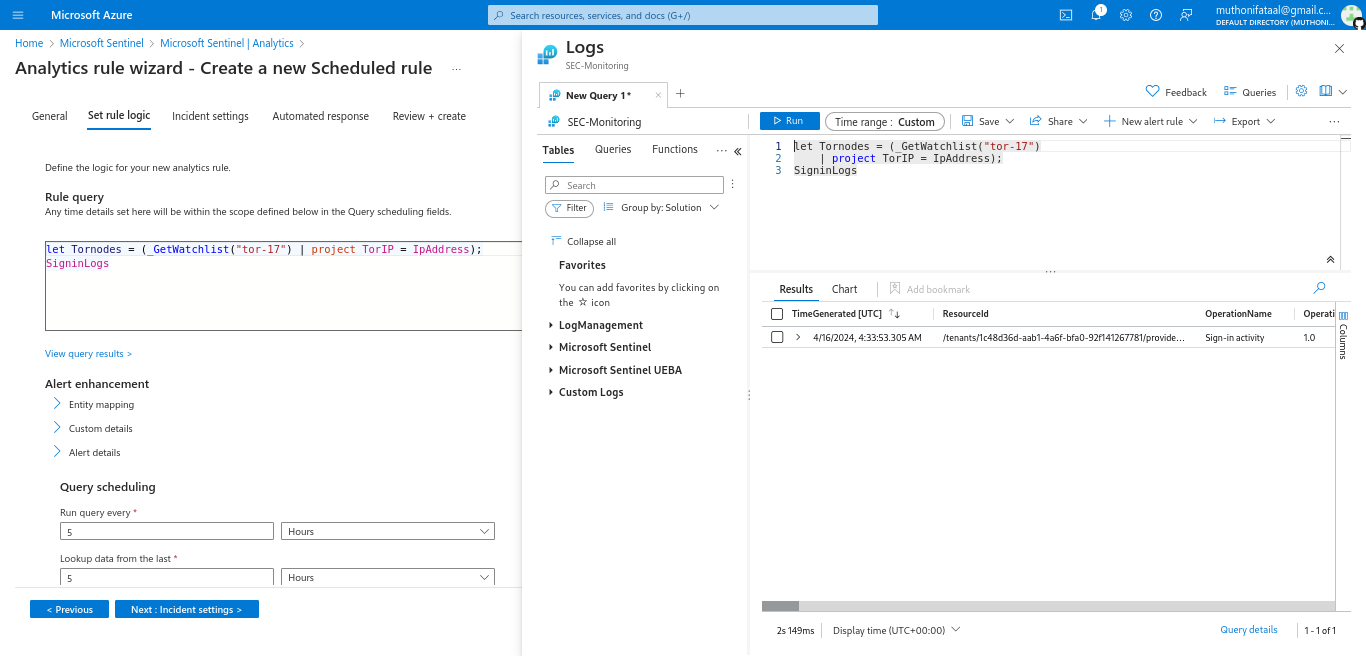
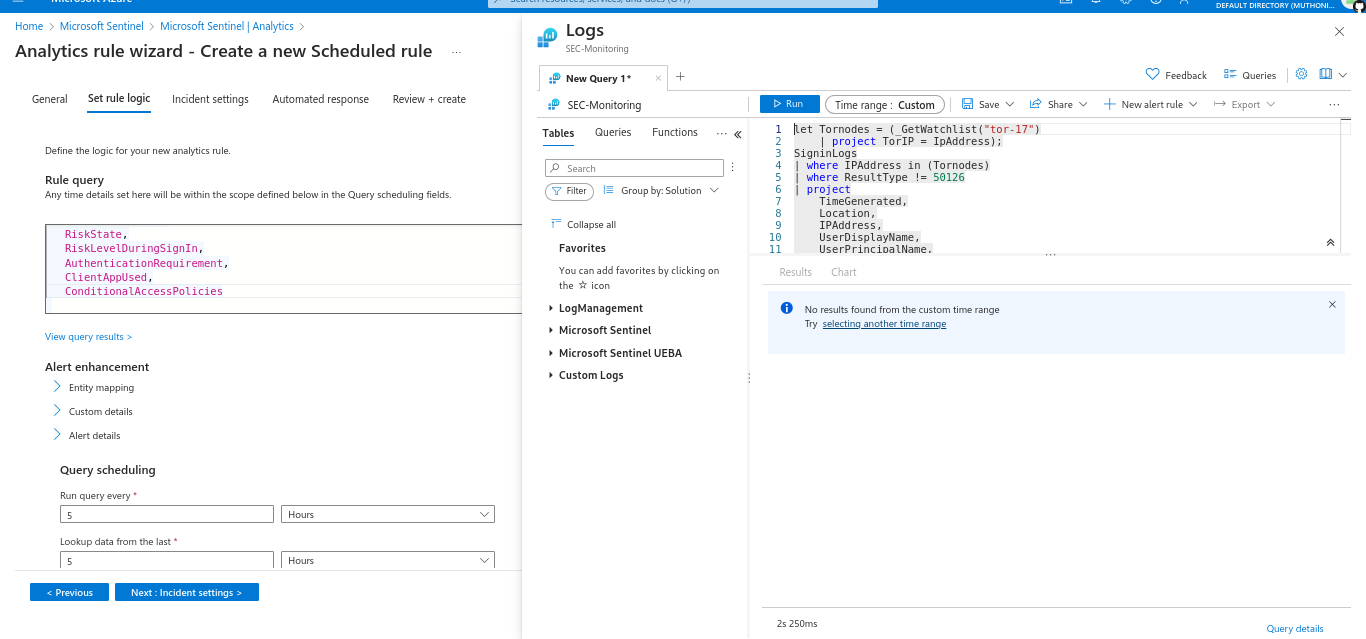
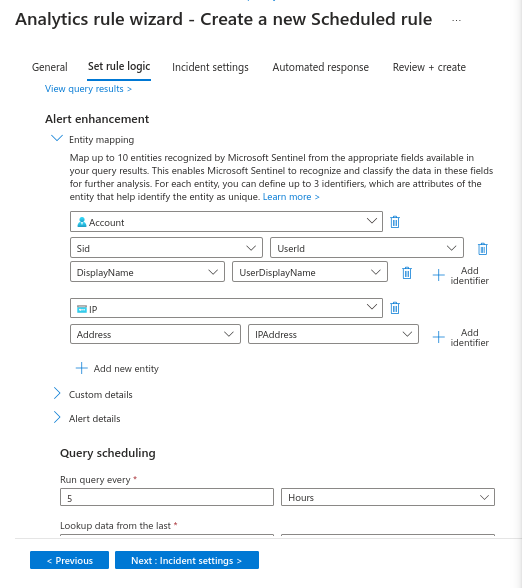
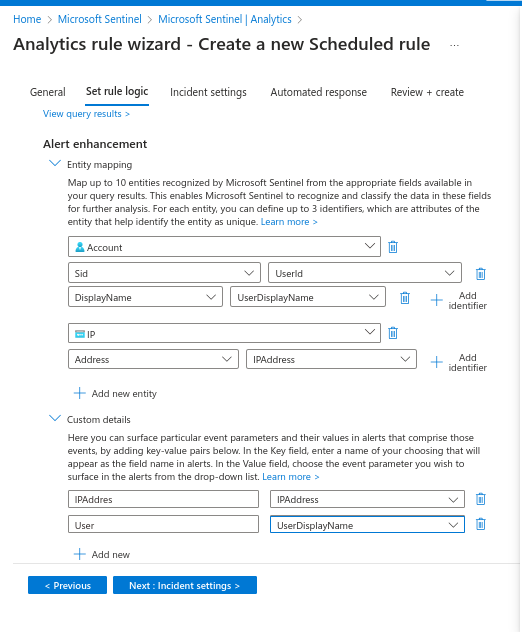
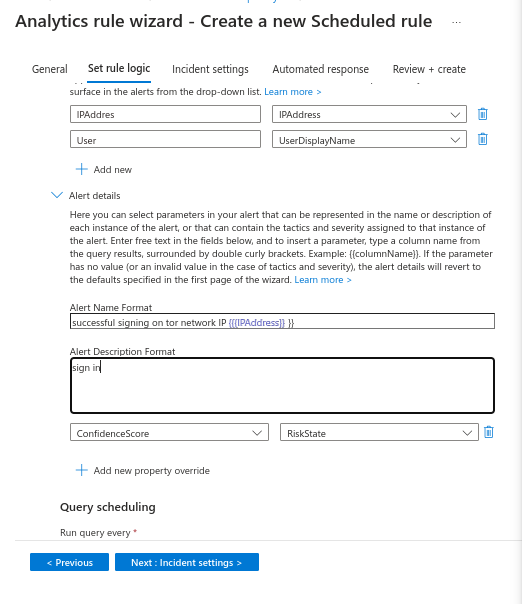
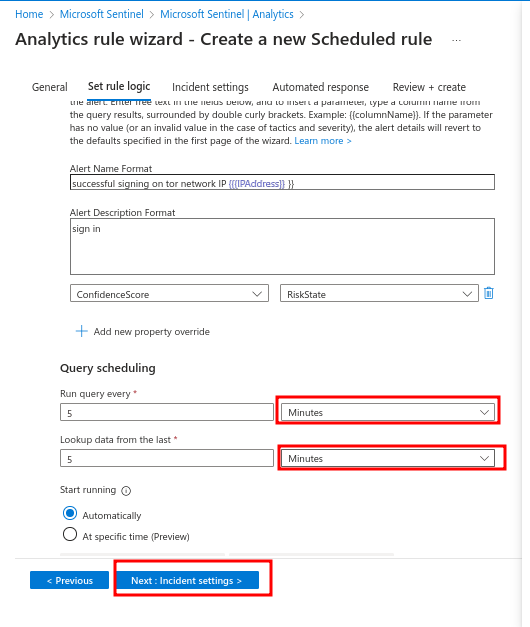
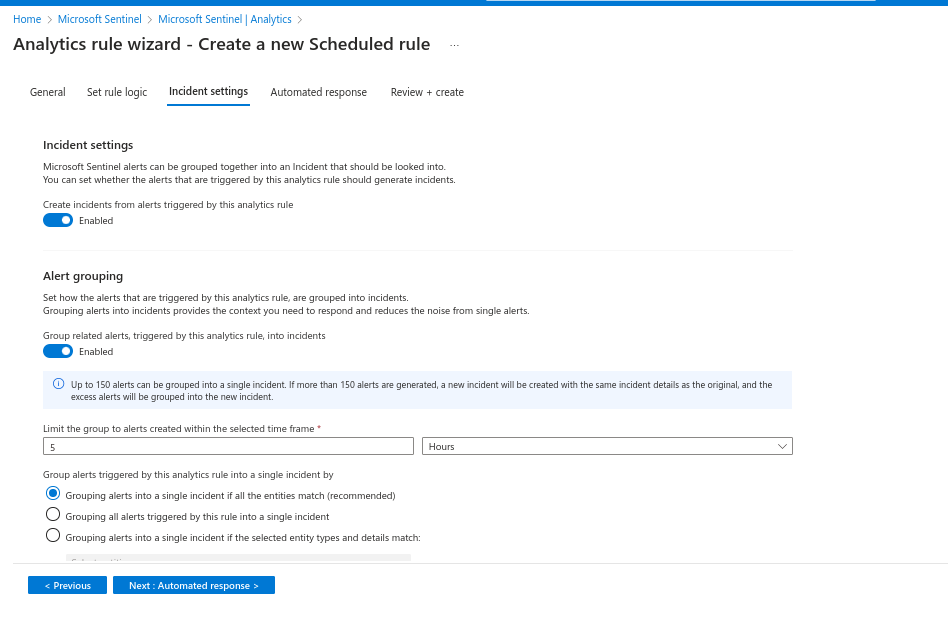
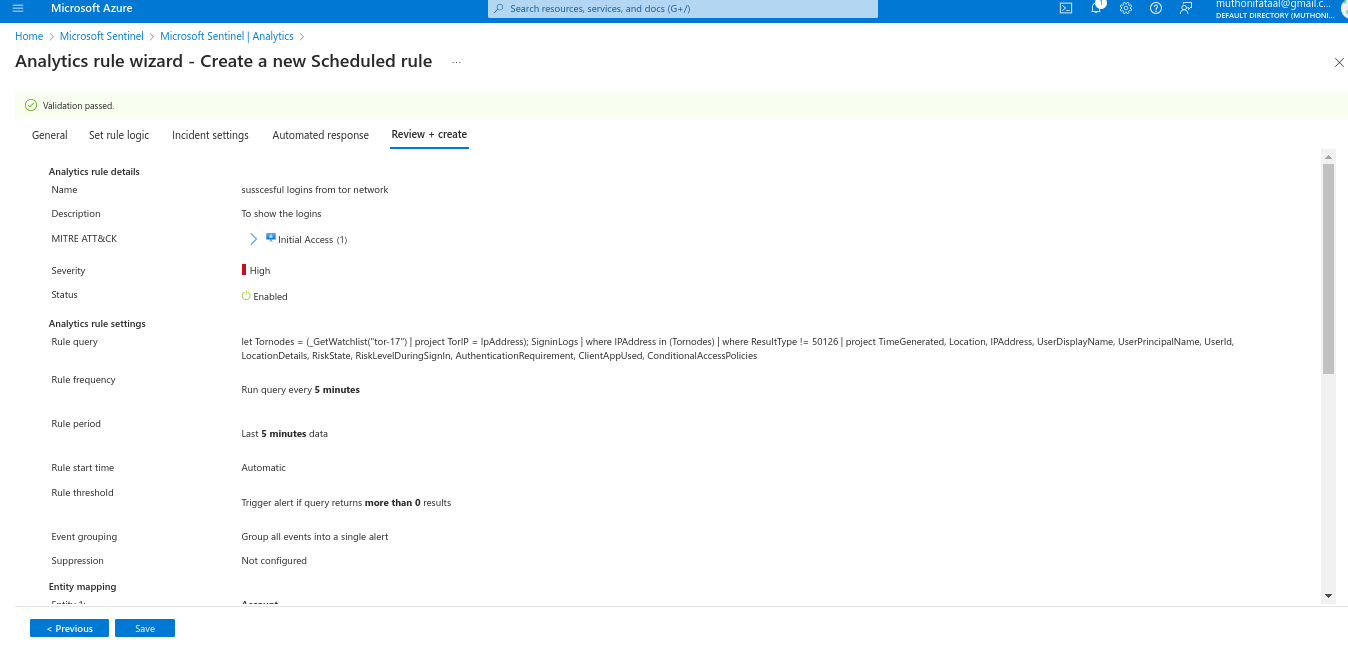
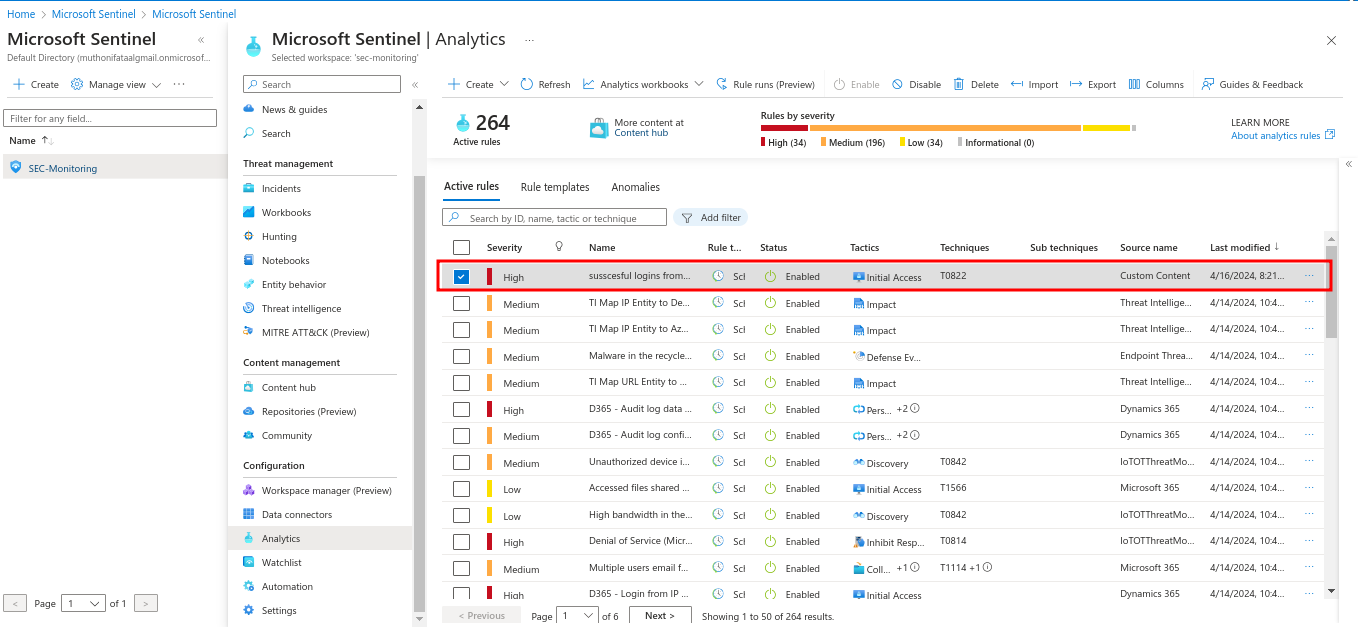
Create Alert Criteria - In the Microsoft Sentinel dashboard, set up alert rules based on the company’s or your security specifications, such as identifying erroneous network activities and suspicious logins.
Create Log Analytics Workspace
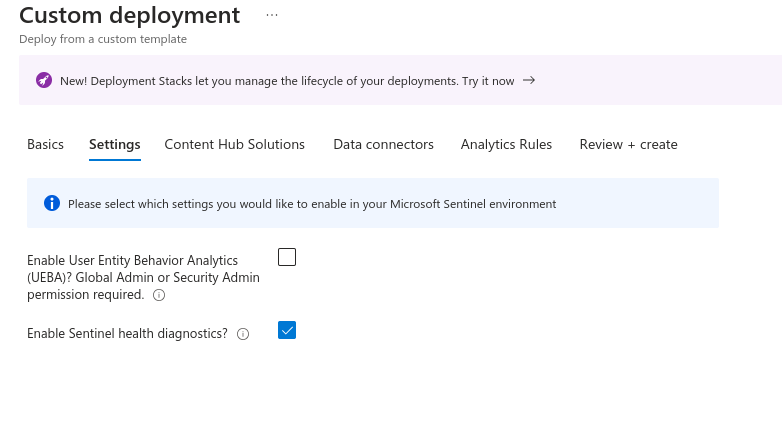
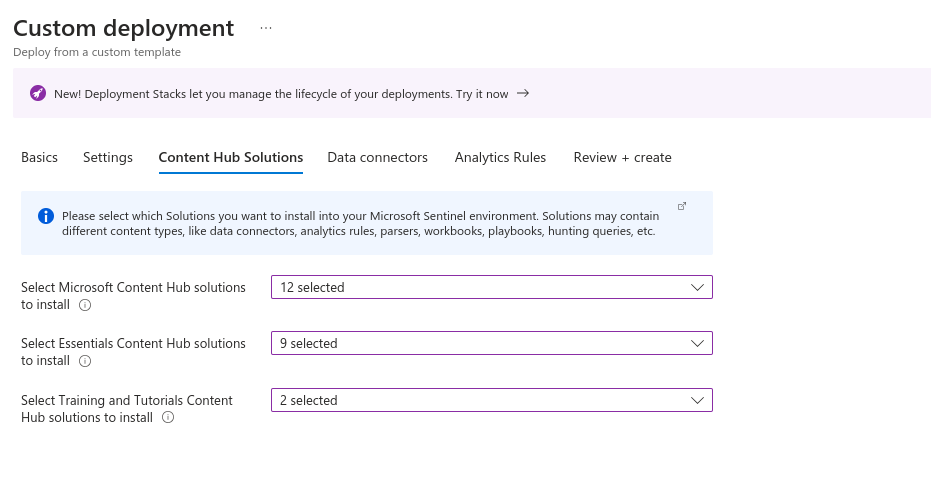
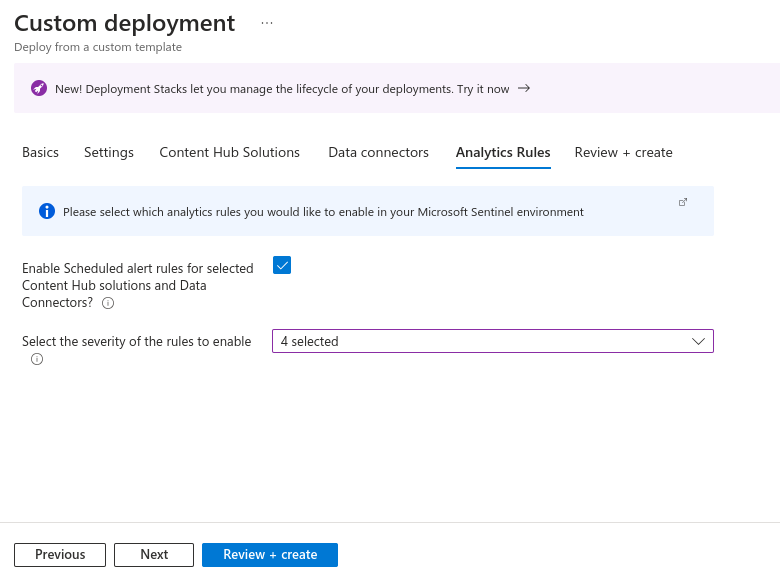
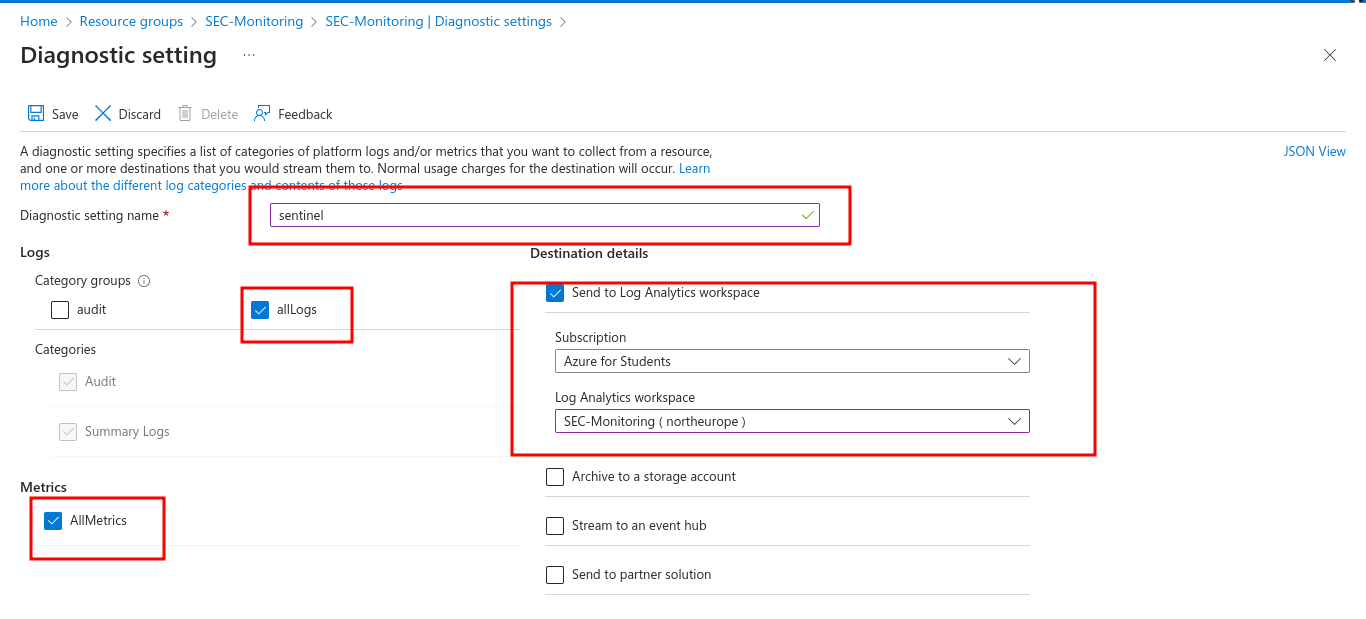
Step 2: Data Ingestion and Configuration
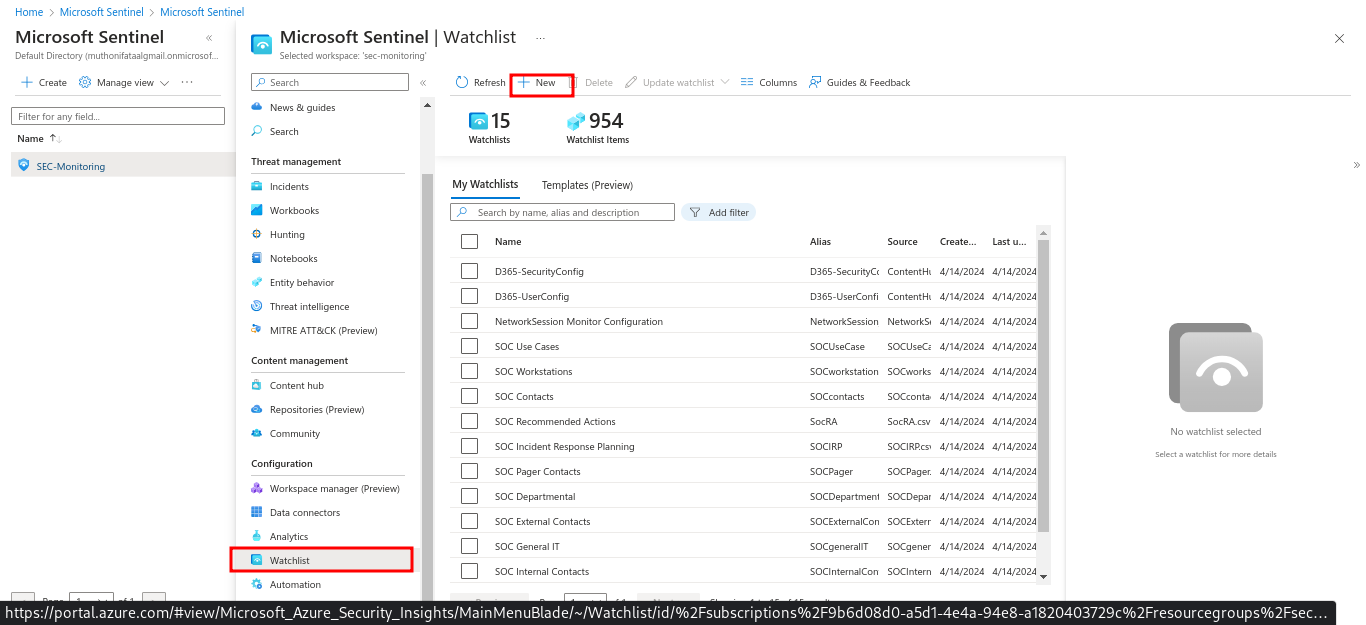
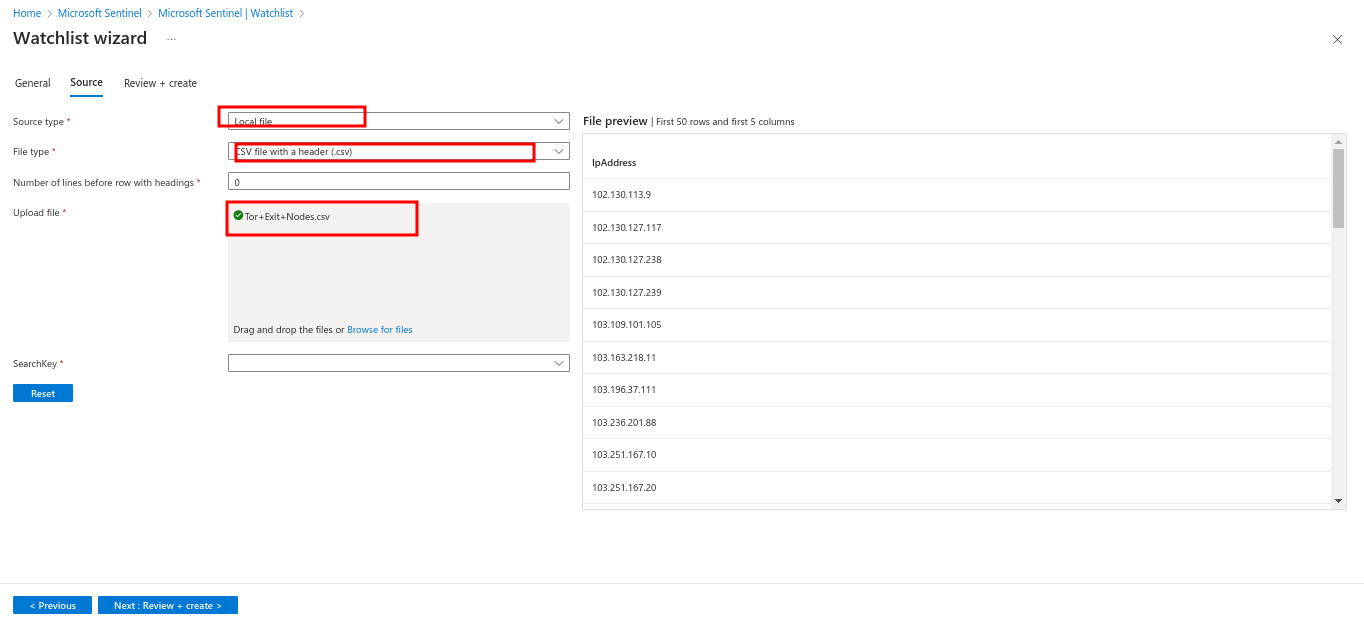
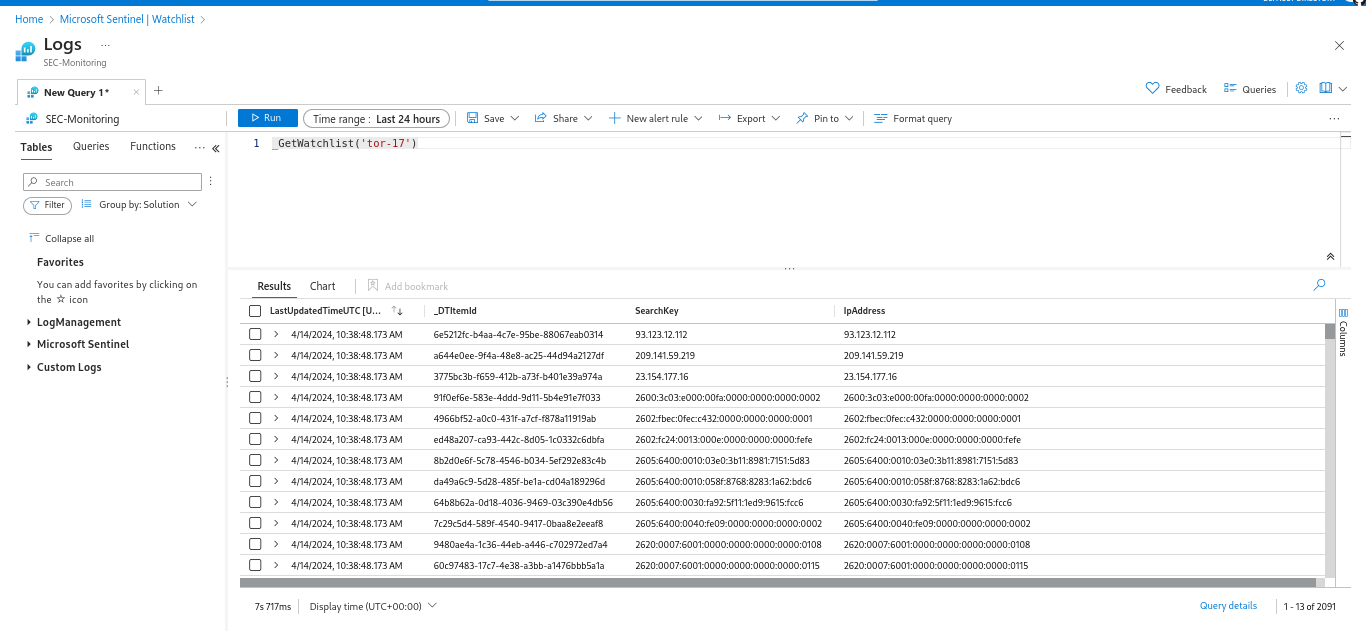
This stage is focused on data ingestion and configuration for Microsoft Sentinel. You will be required to connect Sentinel to various data sources, including Azure services, on-premises systems, and third-party applications.I tailored the log-collecting parameters to our specific monitoring requirements, determining which logs to ingest and the collection frequency, turned on threat intelligence feeds to integrate external threat information, enhancing our ability to detect and respond to potential security incidents, and lastly I created Sentinel dashboards and views to provide relevant insights into our security posture, enabling quick identification and prioritization of security events.
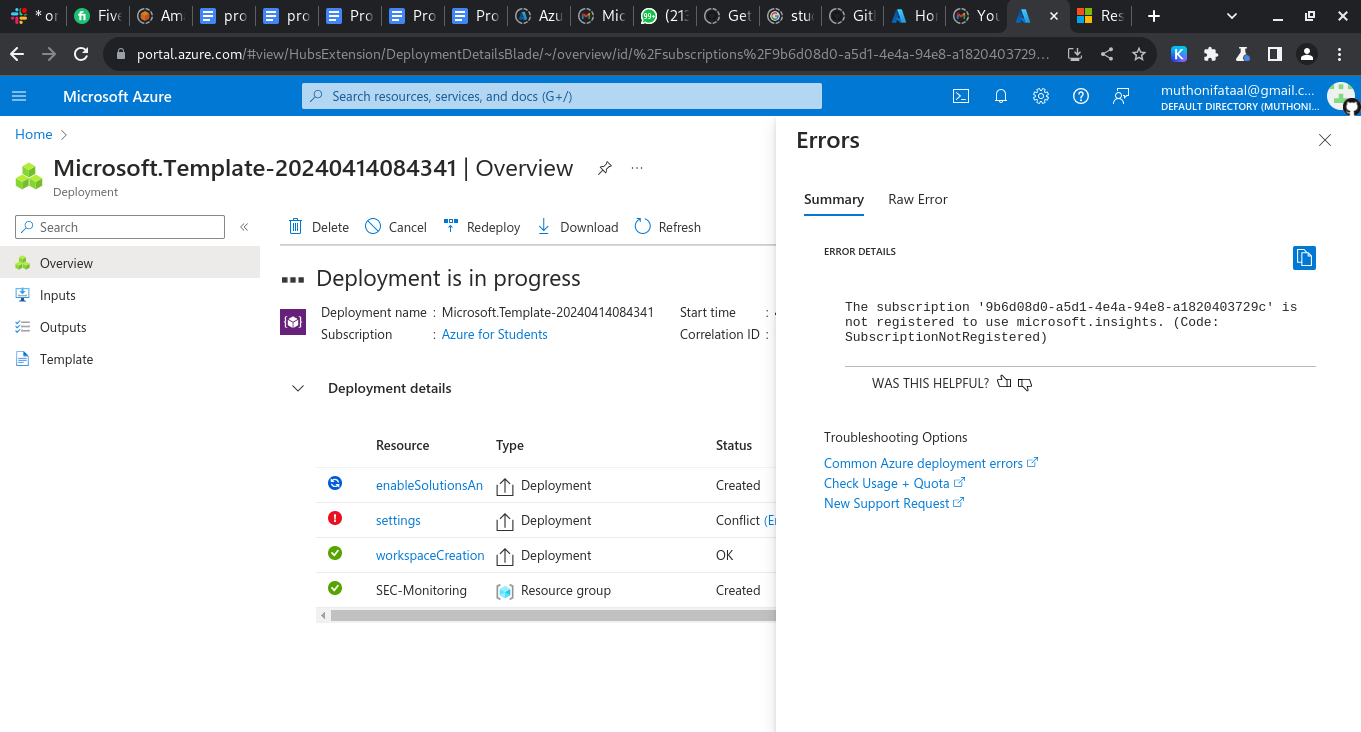
In case of deployment issues, I followed the troubleshooting guide available at Azure Resource Manager Troubleshooting. Azure provides a solution to every error.
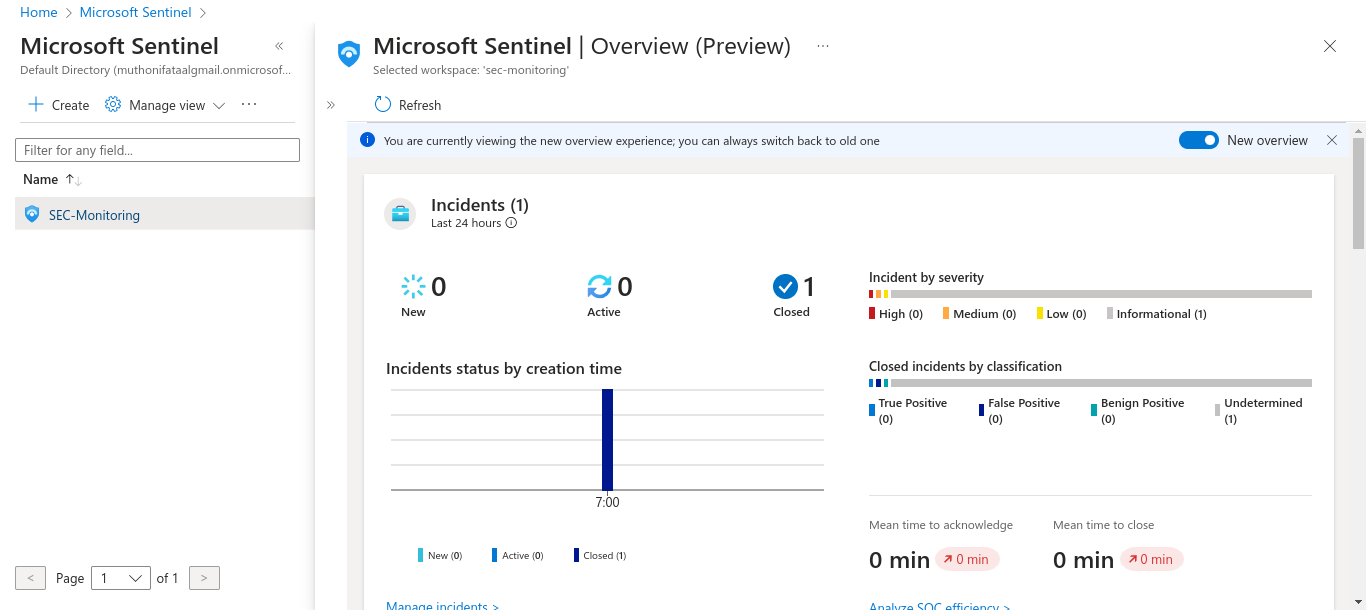
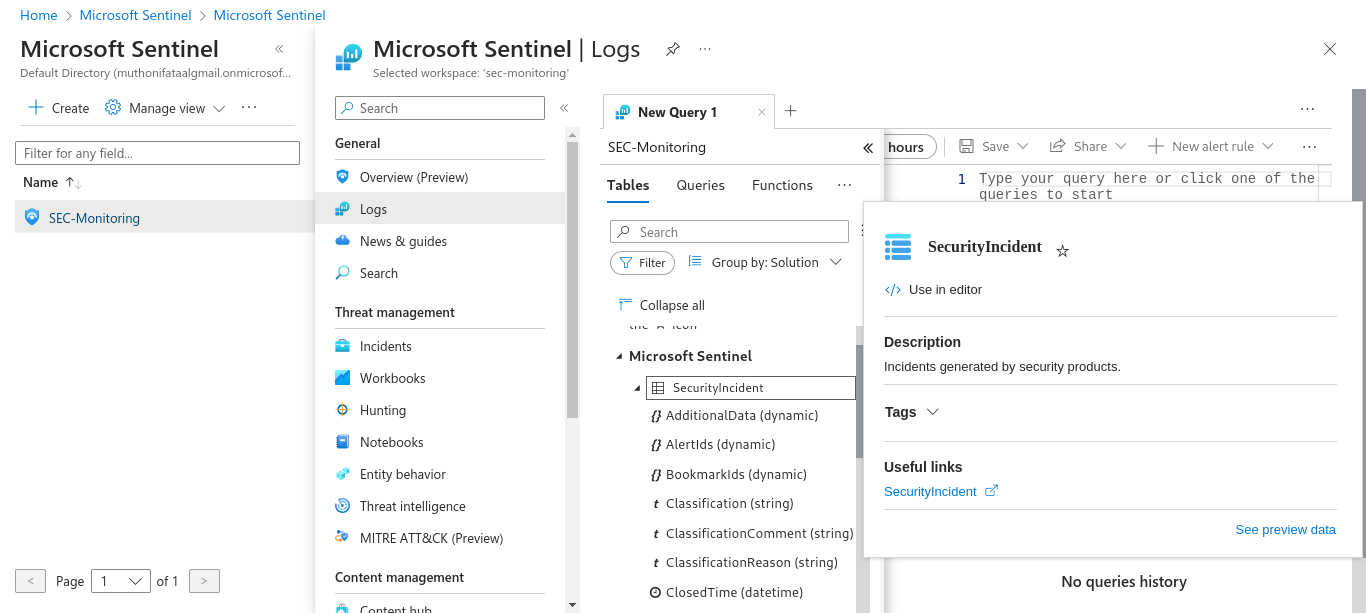
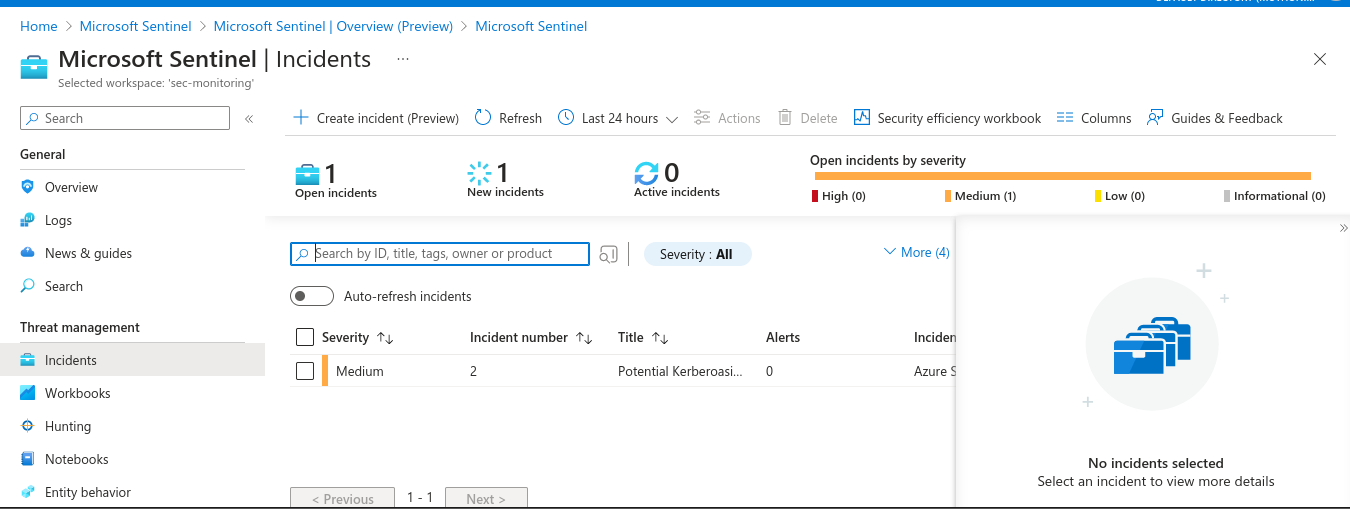
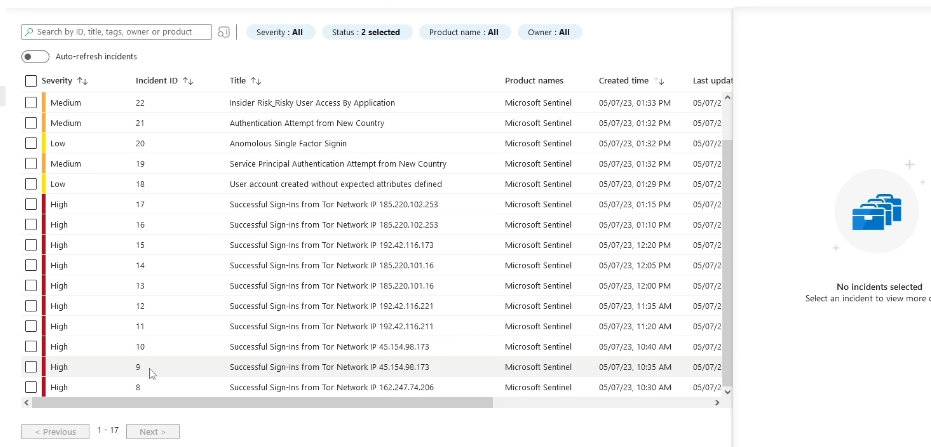
Step 3: Incident Detection and Response
In this stage you will review the security events logged by the system, using machine learning and advanced analytics to identify potential threats and anomalies. I created incident processes detailing the steps to handle various security issues, streamlining the response process, configured automated response actions to enable swift reactions to specific incidents, reducing manual intervention and response times, and performed in-depth security incident analyses using Sentinel’s features to gather information, determine root causes, and resolve issues effectively.
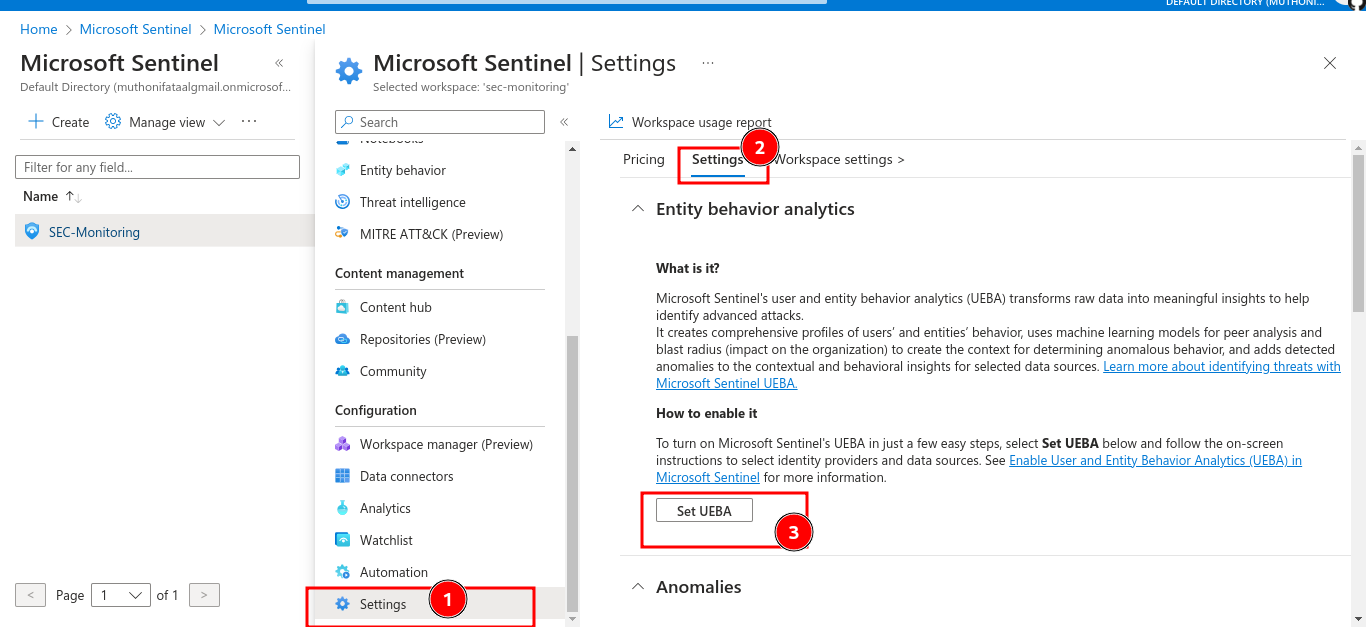
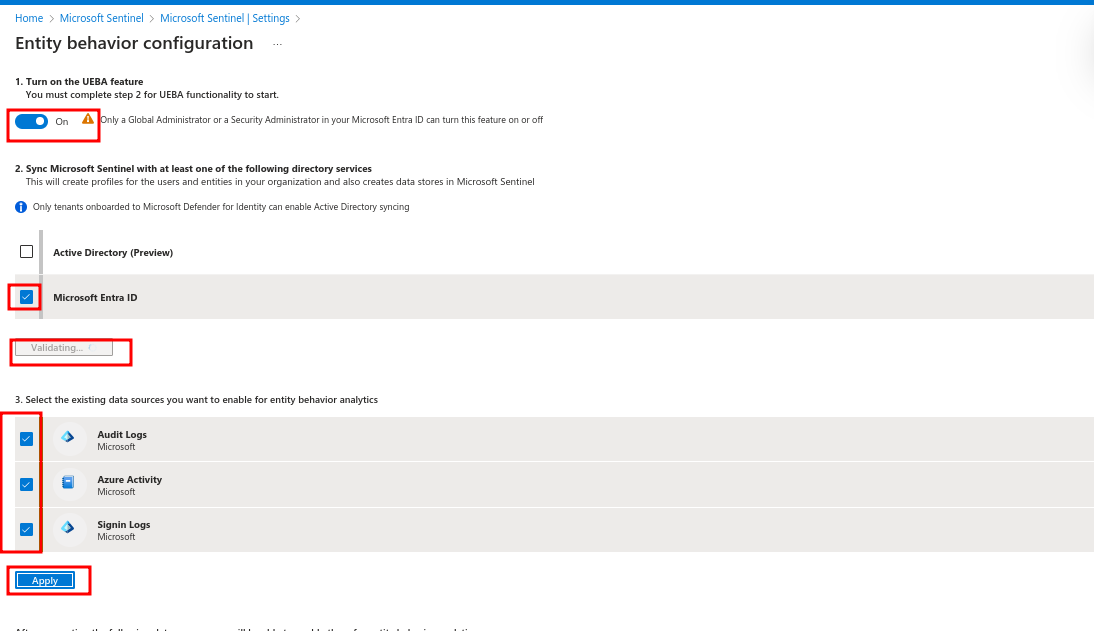
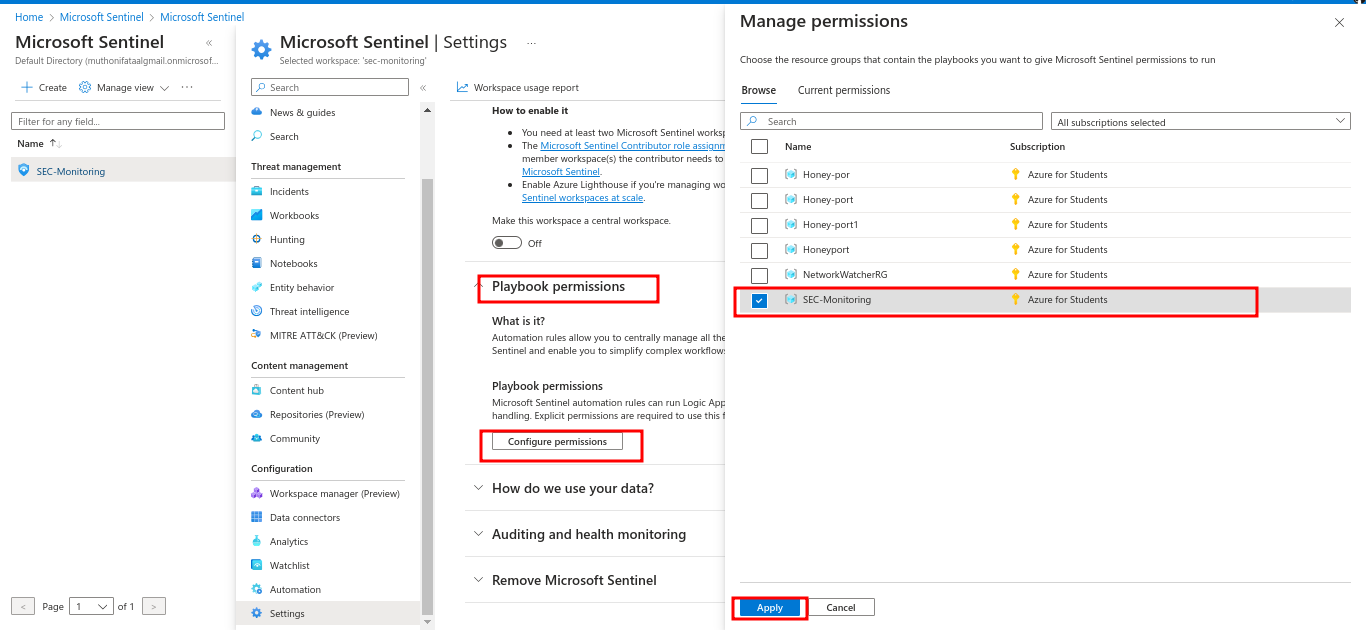
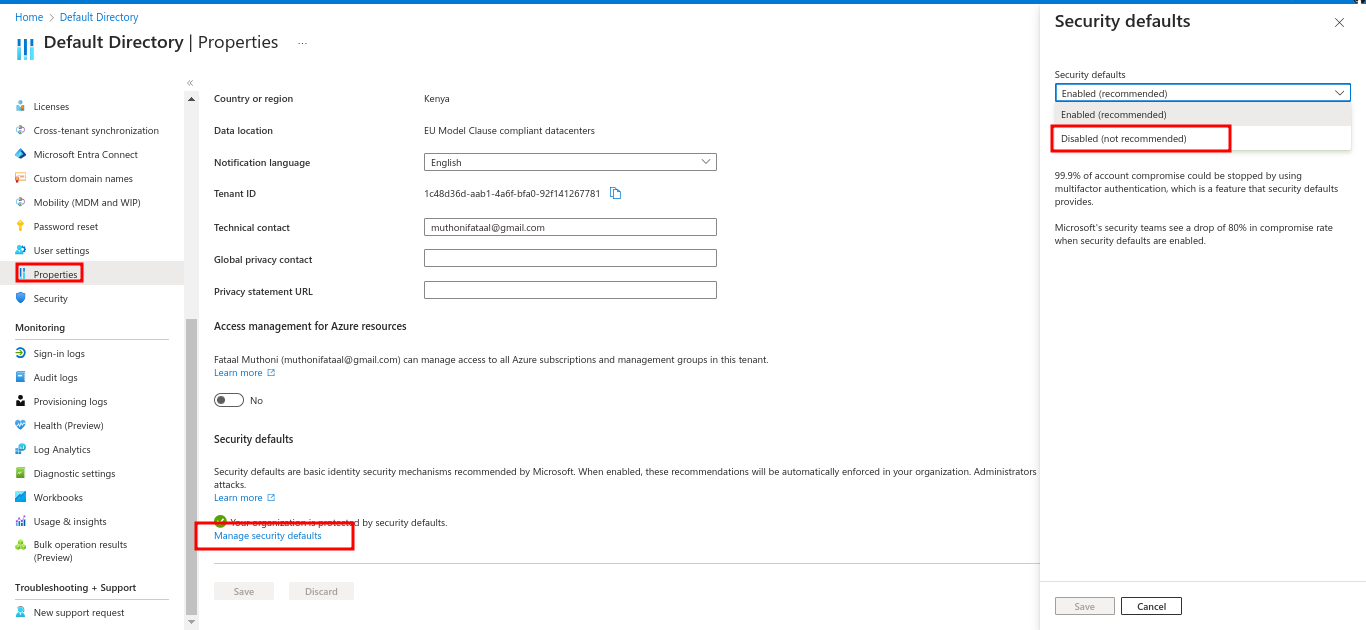
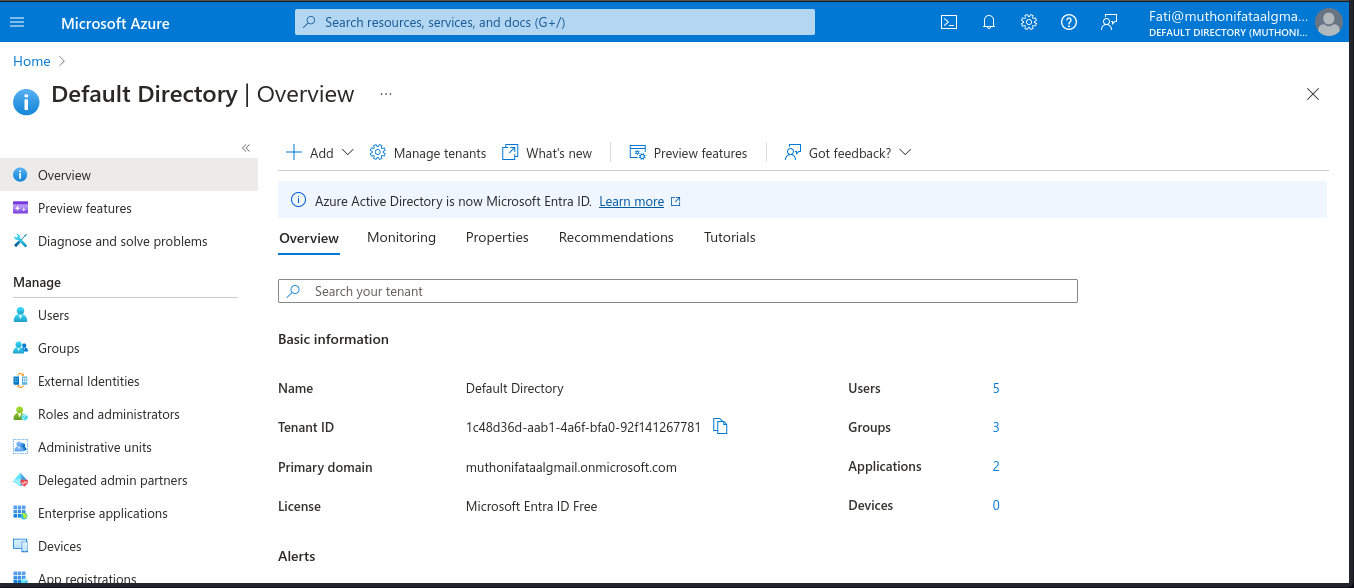
Step 4: Integration with Azure Security Services
In this stage you will integrate Microsoft Sentinel with various Azure security services. I utilized Azure Security Center’s threat intelligence and advanced threat prevention capabilities, enhanced user and entity data integration with Azure Active Directory, facilitating more contextually rich investigations and threat hunting, and then set up Sentinel playbooks to automate response activities and orchestrate incident response processes across our Azure infrastructure.
Step 5: Continuous Monitoring and Optimization
In this stage, the focus is on continuous monitoring and optimization. I created regular queries to assess our security posture and identify potential risks or vulnerabilities. Reviewing and refining the alert policies ensured they aligned with the the security priorities and risk tolerance. Additionally, I conducted capacity planning and scaling to ensure our Sentinel deployment could handle increasing data volumes and maintain peak performance over time.
SIEM-Integration-with-Artificial-Intelligence-ChatGPT
Installing and configuring ChatGPT in Microsoft Sentinel
Overview
Let’s explores the integration of ChatGPT with Microsoft Sentinel SIEM to enhance threat detection, streamline response times, and strengthen security analytics. By leveraging advancements in natural language processing, I can harness ChatGPT’s capabilities to extract valuable insights from vast security datasets, improving overall cybersecurity operations. The guide covers the installation and configuration of ChatGPT within Microsoft Sentinel, focusing on developing realistic security scenarios, implementing effective monitoring strategies, and ensuring compliance with regulatory requirements. Through this research, I aim to equip myself and other security professionals with the knowledge to fortify cybersecurity defenses using AI-powered language analysis against evolving threats.
Preparation and Setup Phase
Verify Requirements
Ensure you have Microsoft Sentinel access, a ChatGPT API key, and sufficient Azure resources.
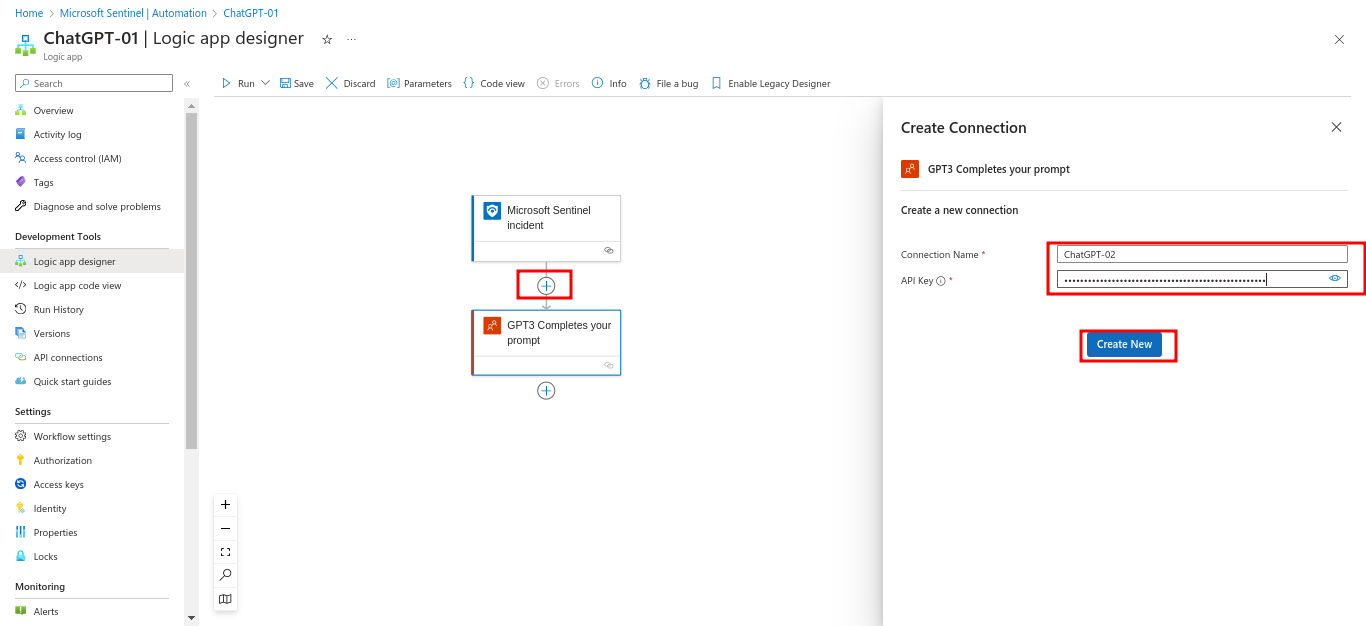
Configuration and Deployment
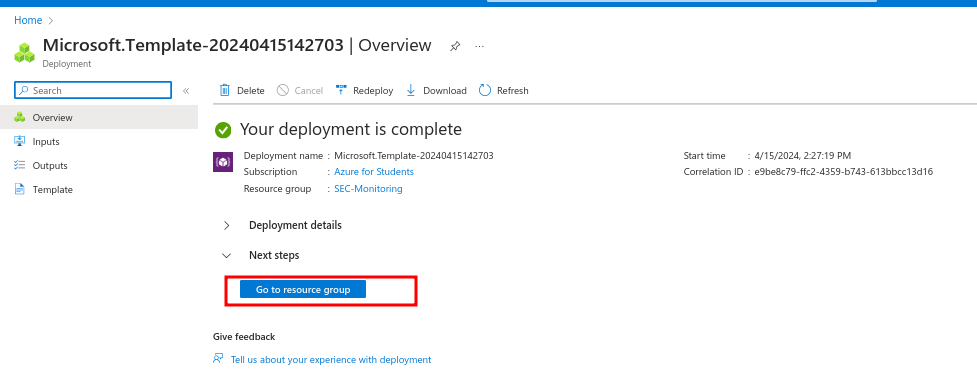
During the Configuration and Deployment phase, I established the necessary infrastructure for integrating ChatGPT with Microsoft Sentinel. This involved setting up the ChatGPT connection, installing Microsoft Sentinel, and configuring the Azure environment. Following Microsoft’s official documentation, I ensured each step aligned with our company’s security requirements. Additionally, I conducted thorough testing to validate the implementation and ensure seamless functionality across the integrated systems. Successful integration in this phase required meticulous attention to detail and adherence to industry best practices.
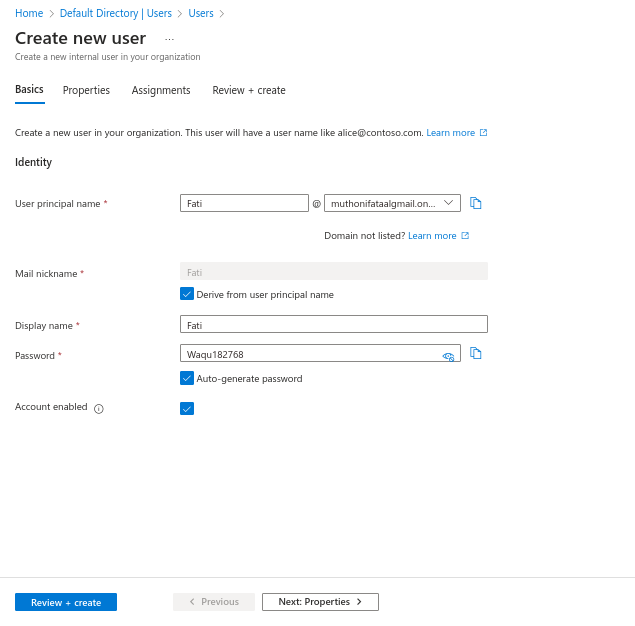
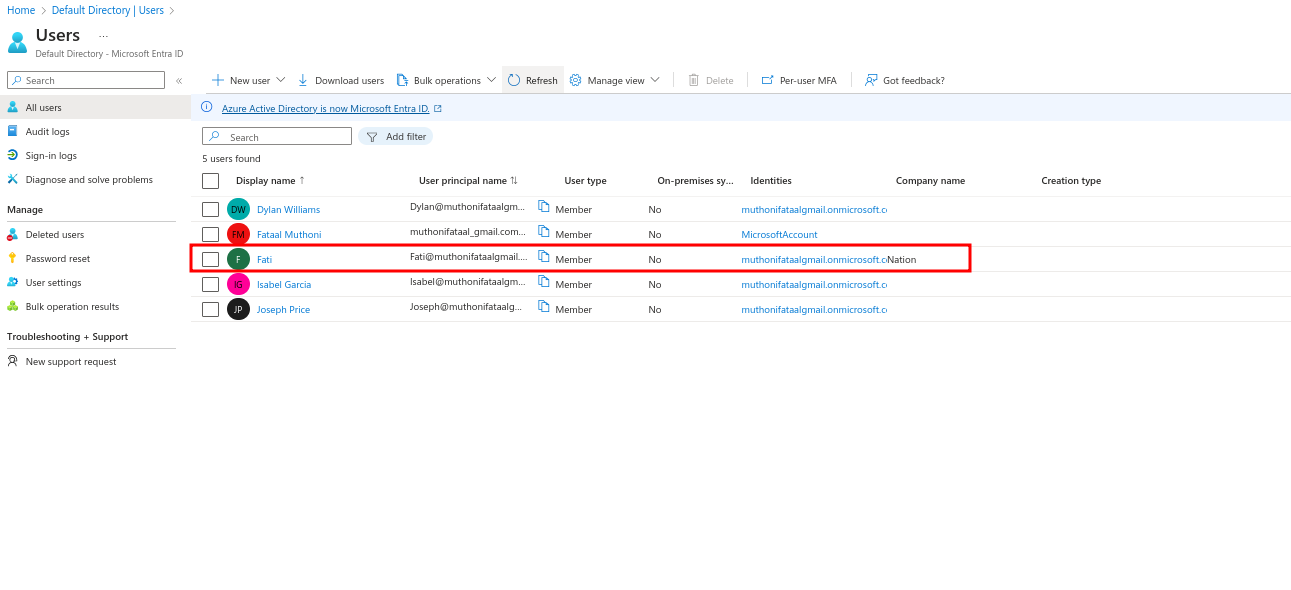
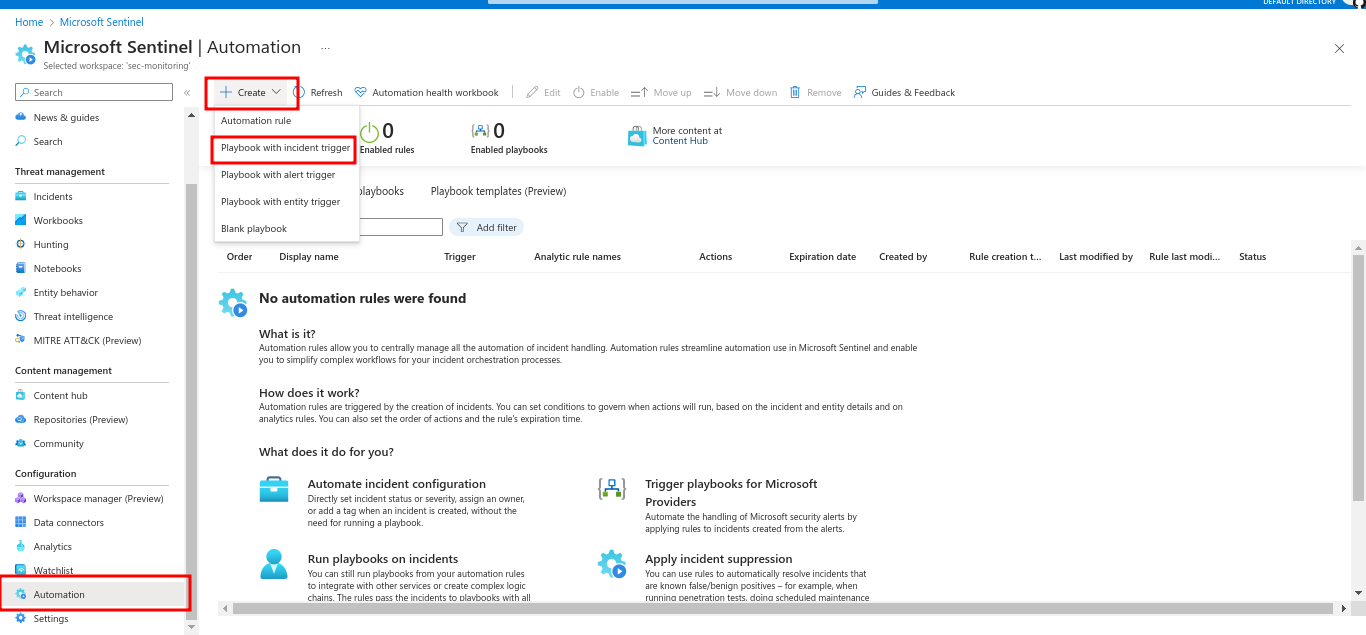
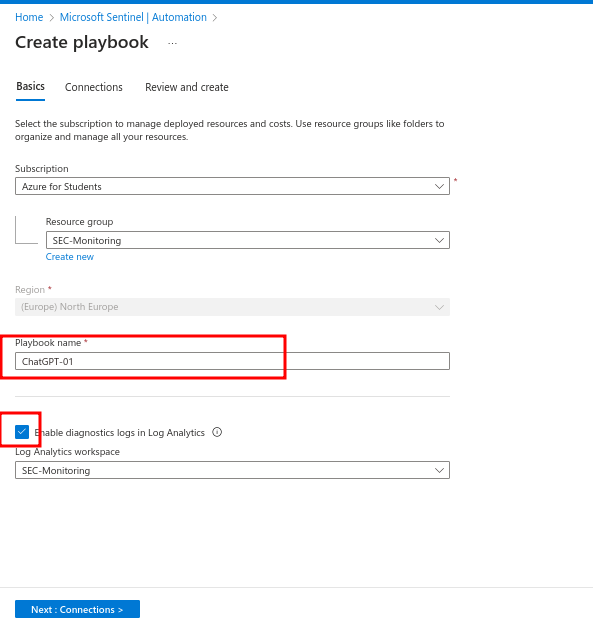
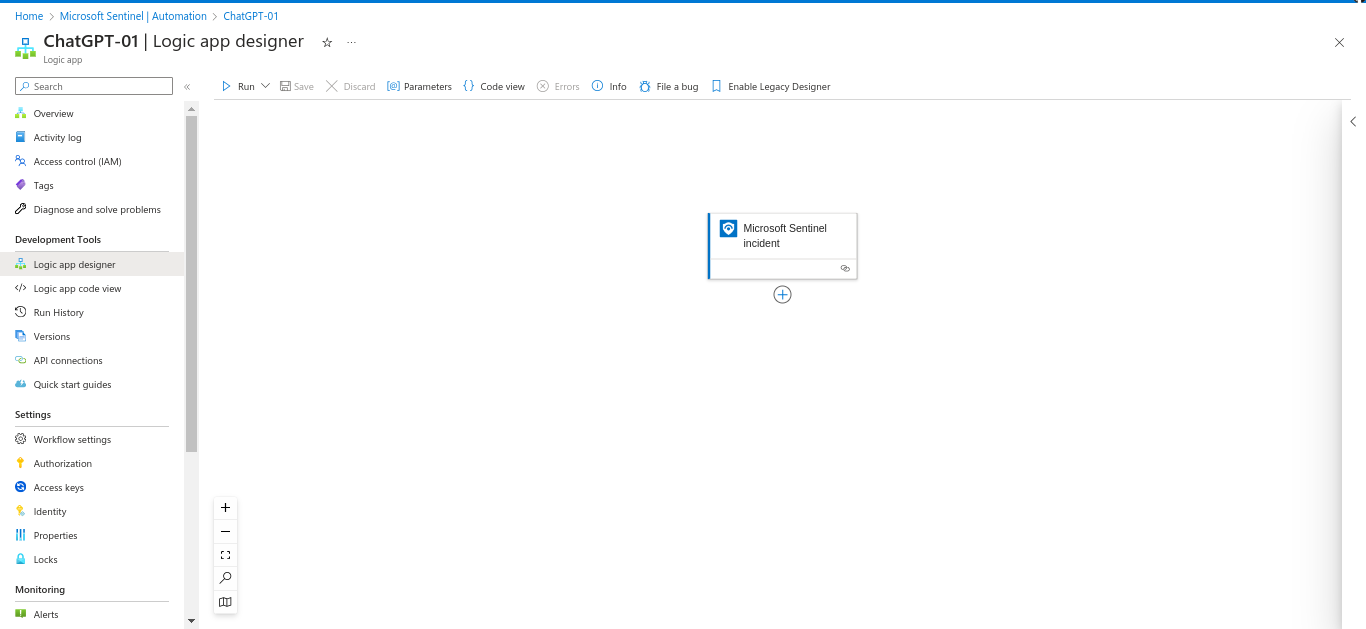
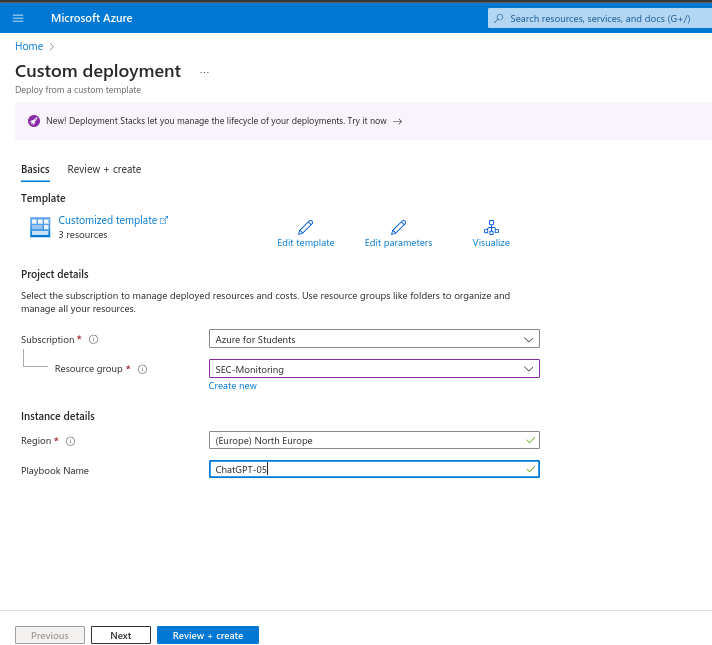
Step 1: Create a playbook for ChatGPT
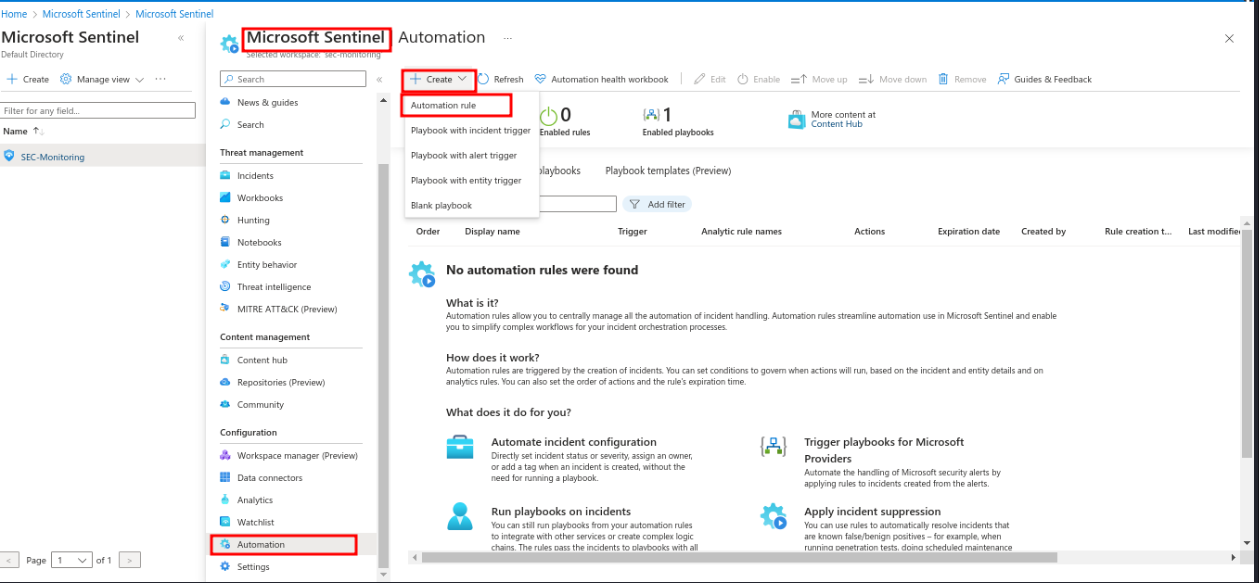
In Sentinel, go to “Automation,” create a Logic App, and add a step to call the ChatGPT API.
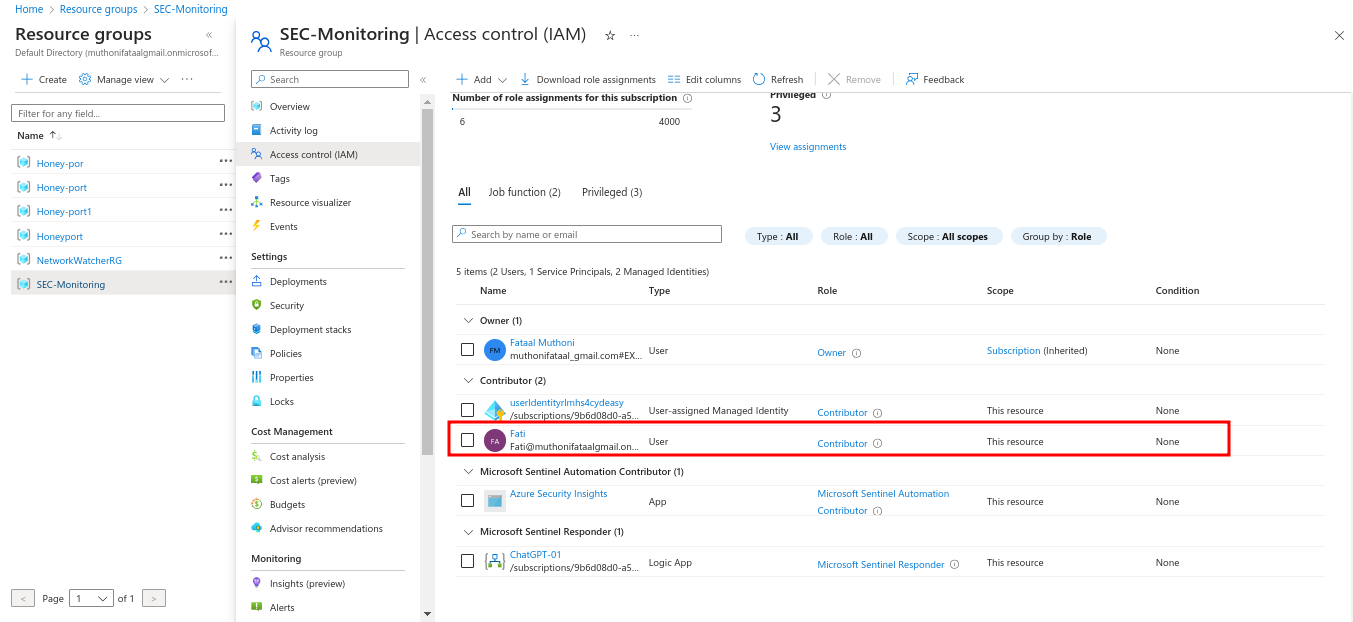
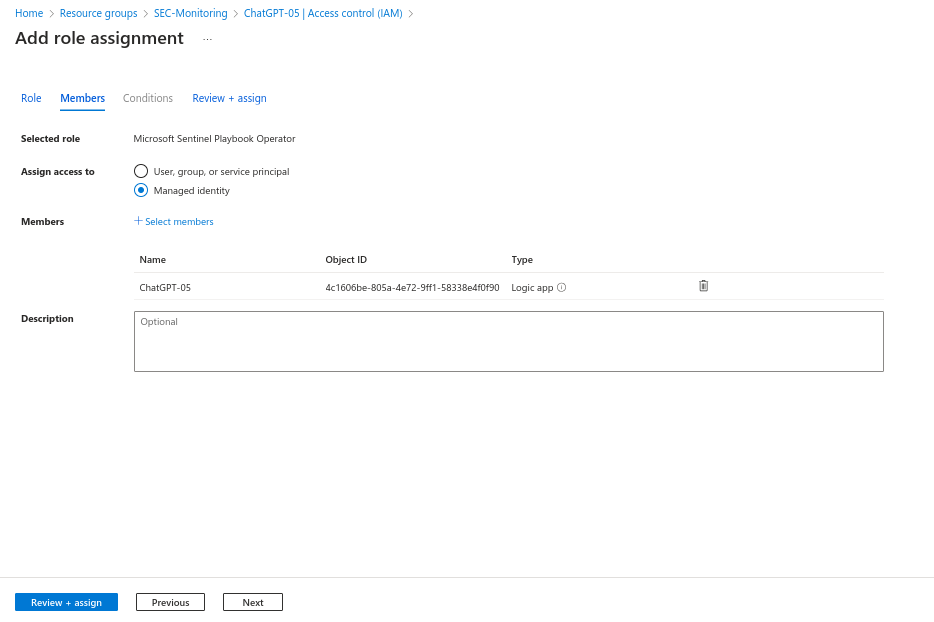
Step 2
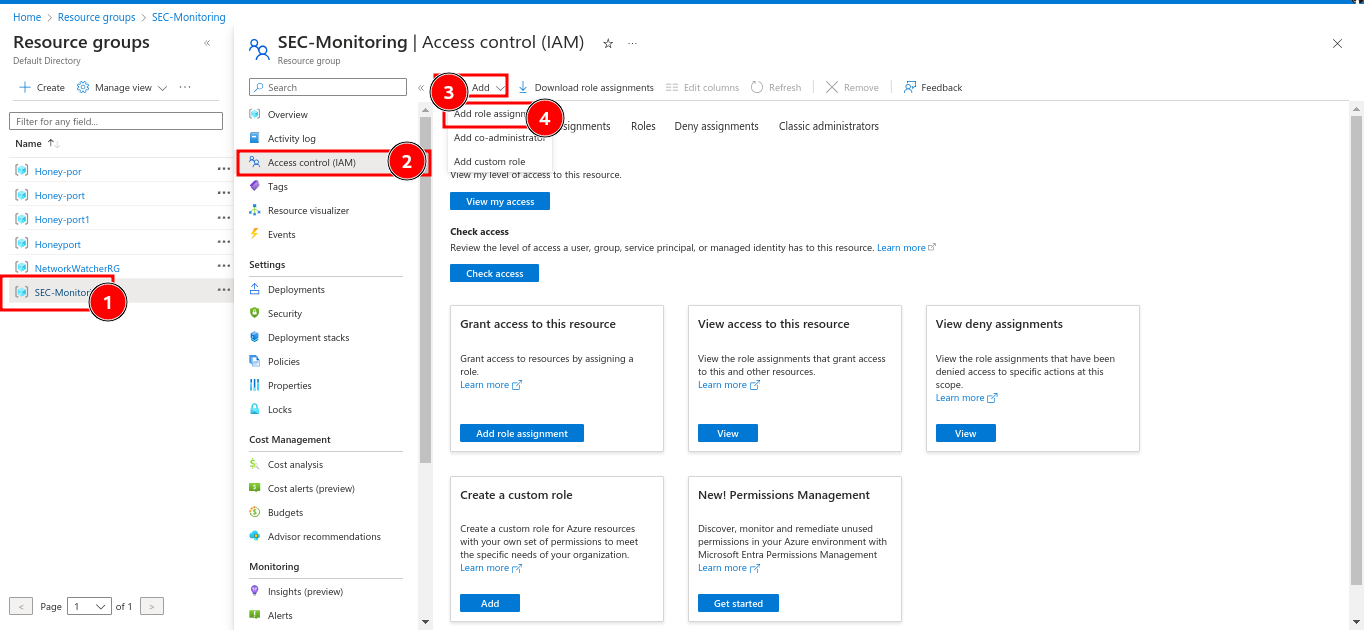
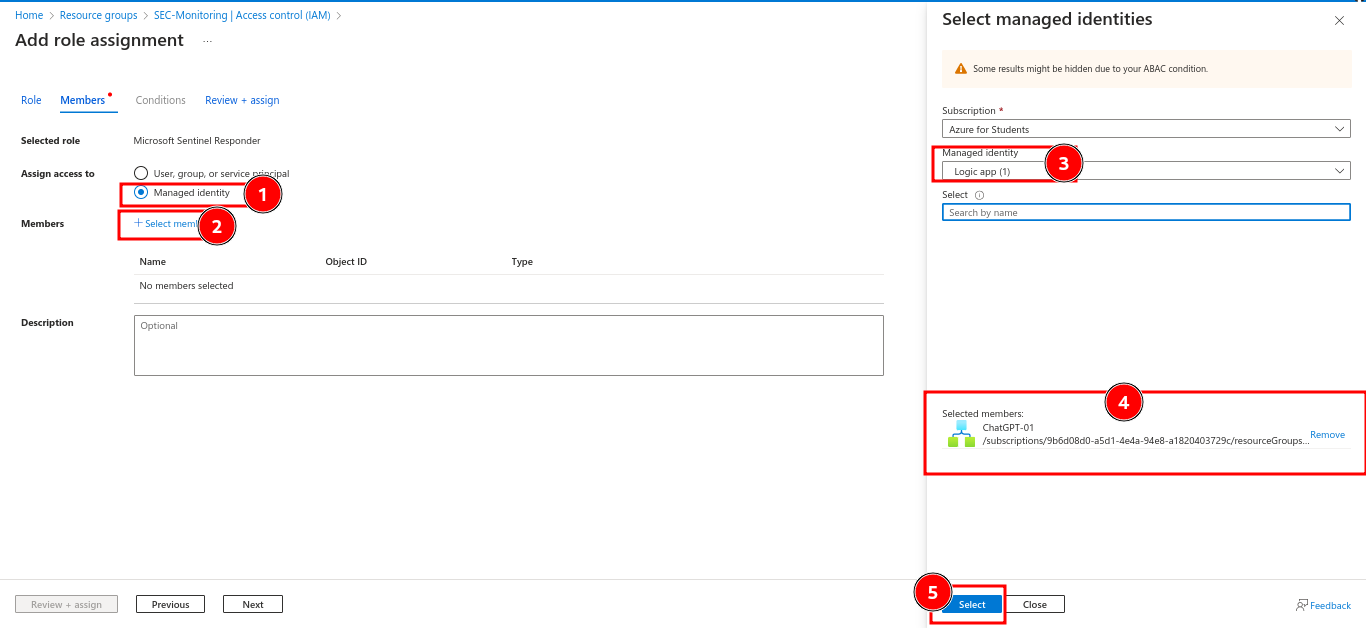
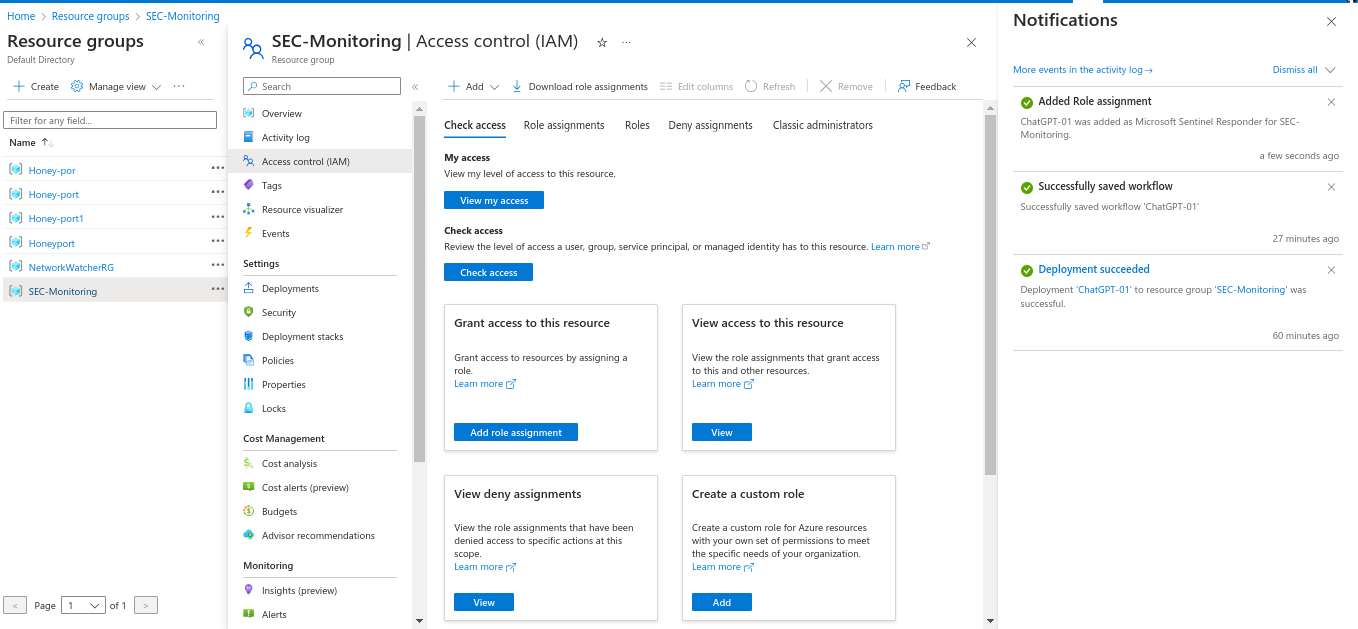
- Assign appropriate permissions
Grant the Logic App permissions to access Sentinel and the ChatGPT API
Testing and Validation Phase
During the Testing and Validation phase, I conducted a comprehensive assessment of the integrated SIEM system’s functionality and performance with ChatGPT. This involved executing various test scenarios to ensure seamless data flow between systems and proper message generation and processing. I closely monitored system logs and performance metrics to detect any anomalies or potential issues. Additionally, I simulated real-world cybersecurity incidents to evaluate the system’s response capabilities. Through rigorous testing and validation, my objective was to confirm the reliability and effectiveness of the integration in enhancing our organization’s cybersecurity posture.
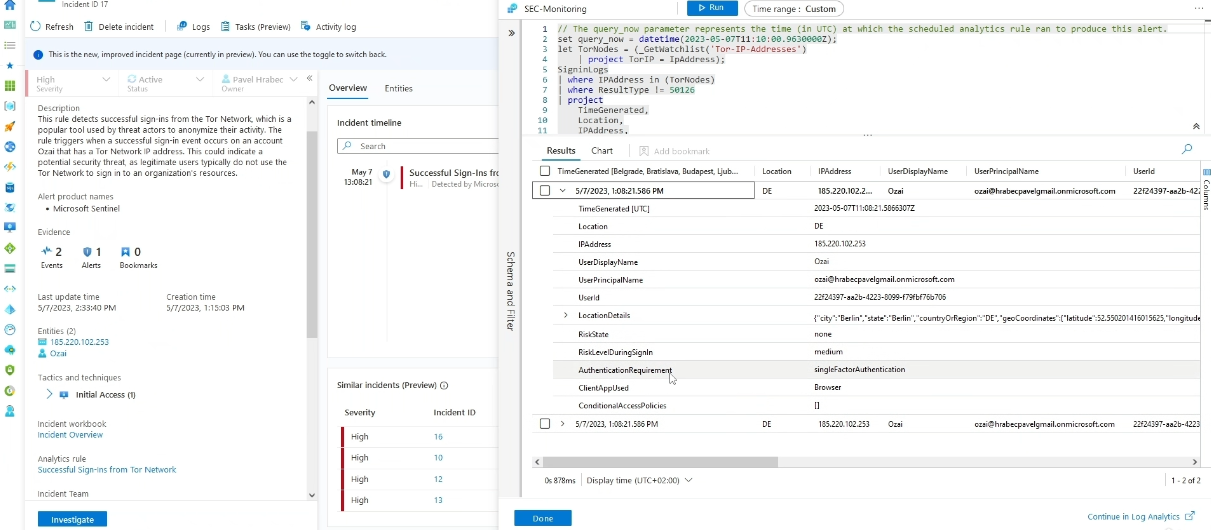
Step 1: Create a cybersecurity incident in SIEM
I simulated a cybersecurity incident to test the system’s detection and response capabilities.
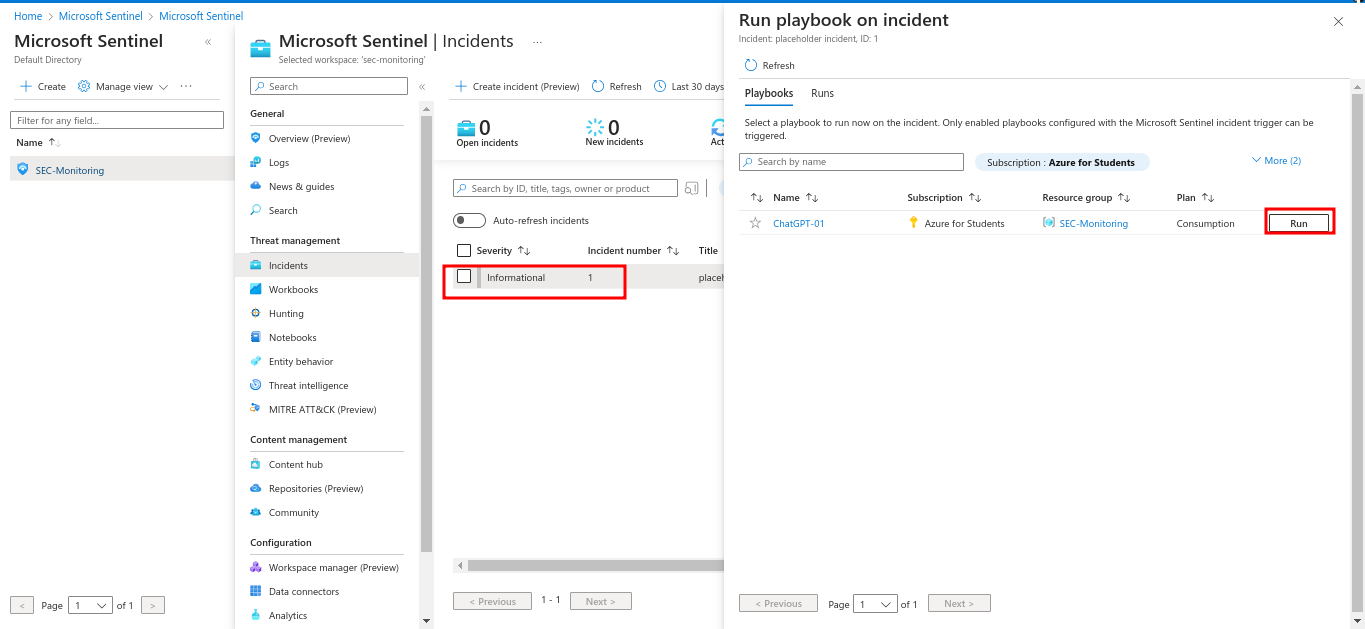
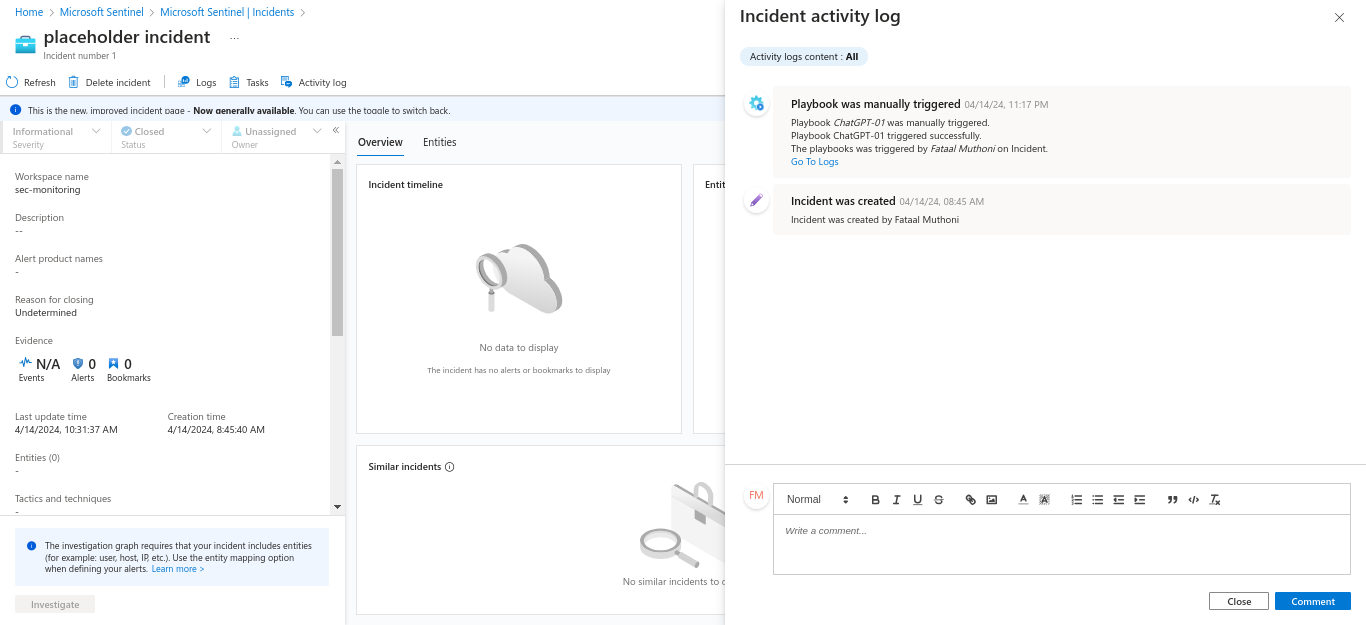
Step 2: Run ChatGPT on cybersecurity incidents
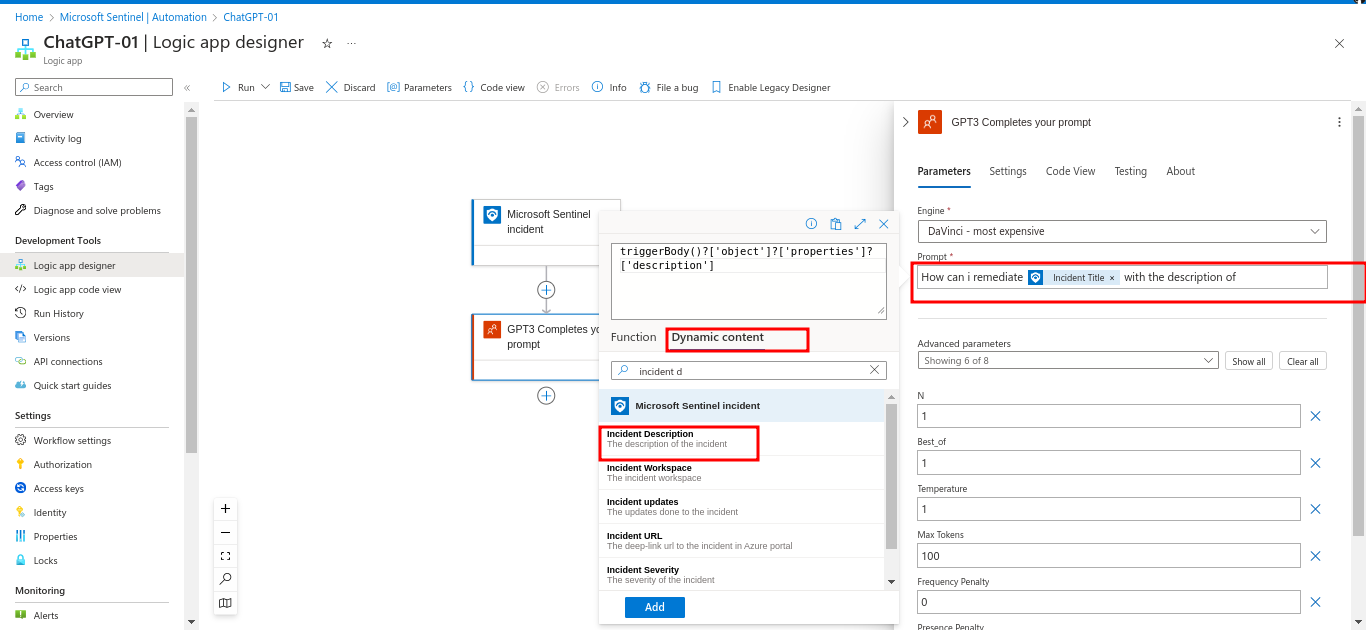
I assessed ChatGPT’s ability to analyze and respond to the simulated incidents by execute the playbook to analyze the incident with ChatGPT
Step 3: Make appropriate adjustments to ChatGPT
I adjusted ChatGPT’s configuration based on the results to optimize its performance.
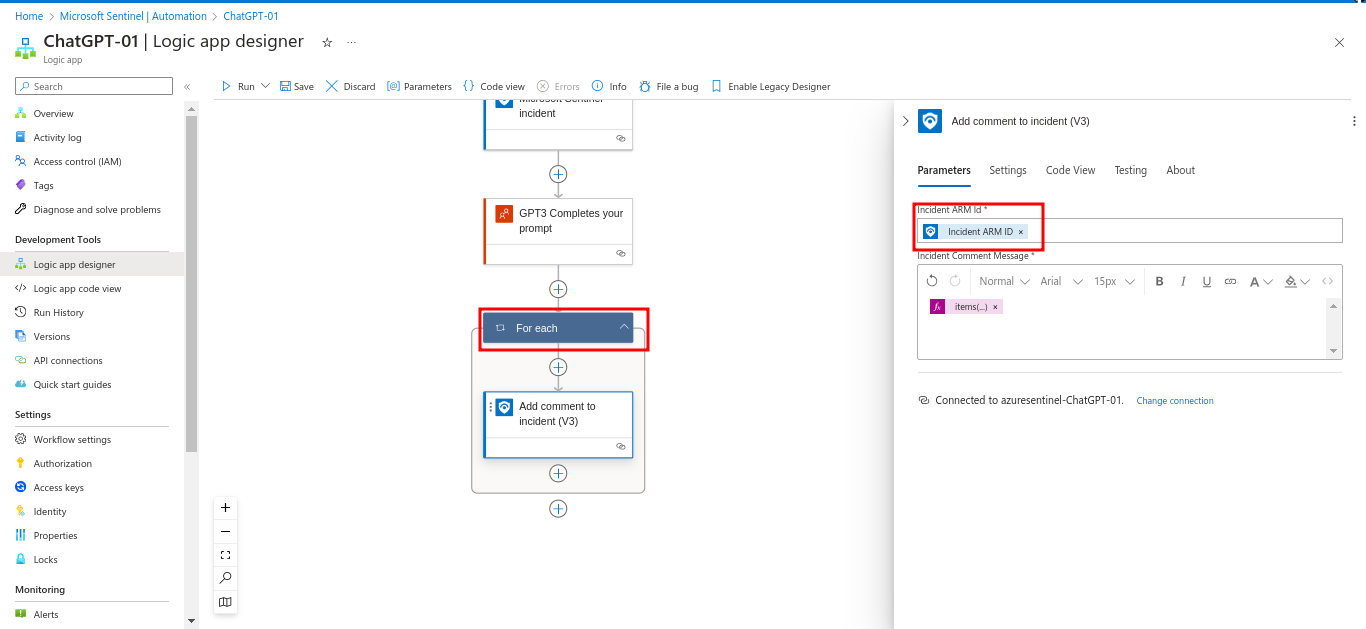
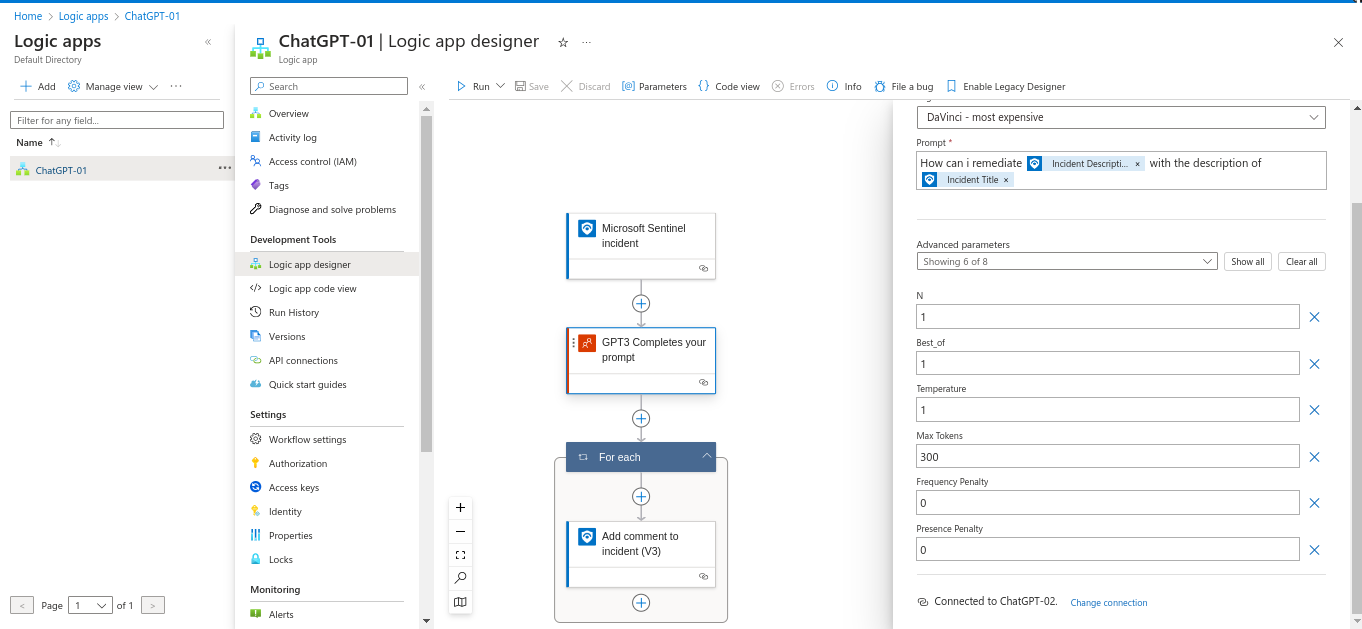
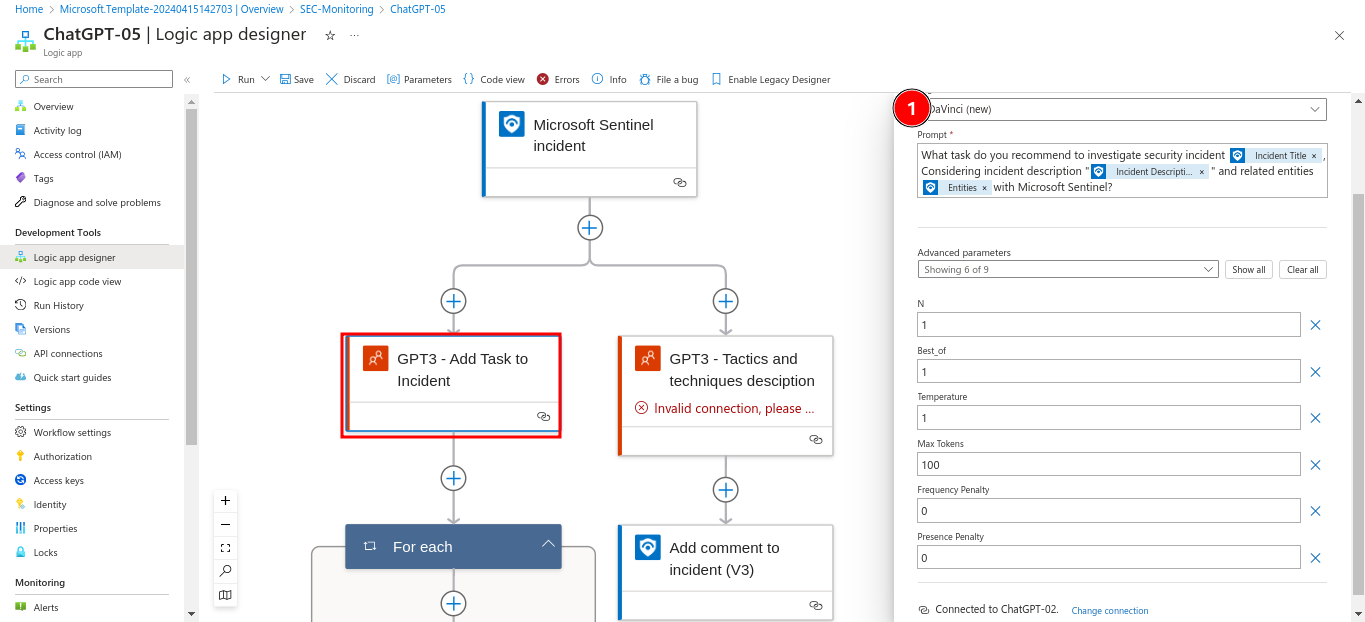
The Logic App editor with an updated “HTTP” action, showing a refined ChatGPT prompt. 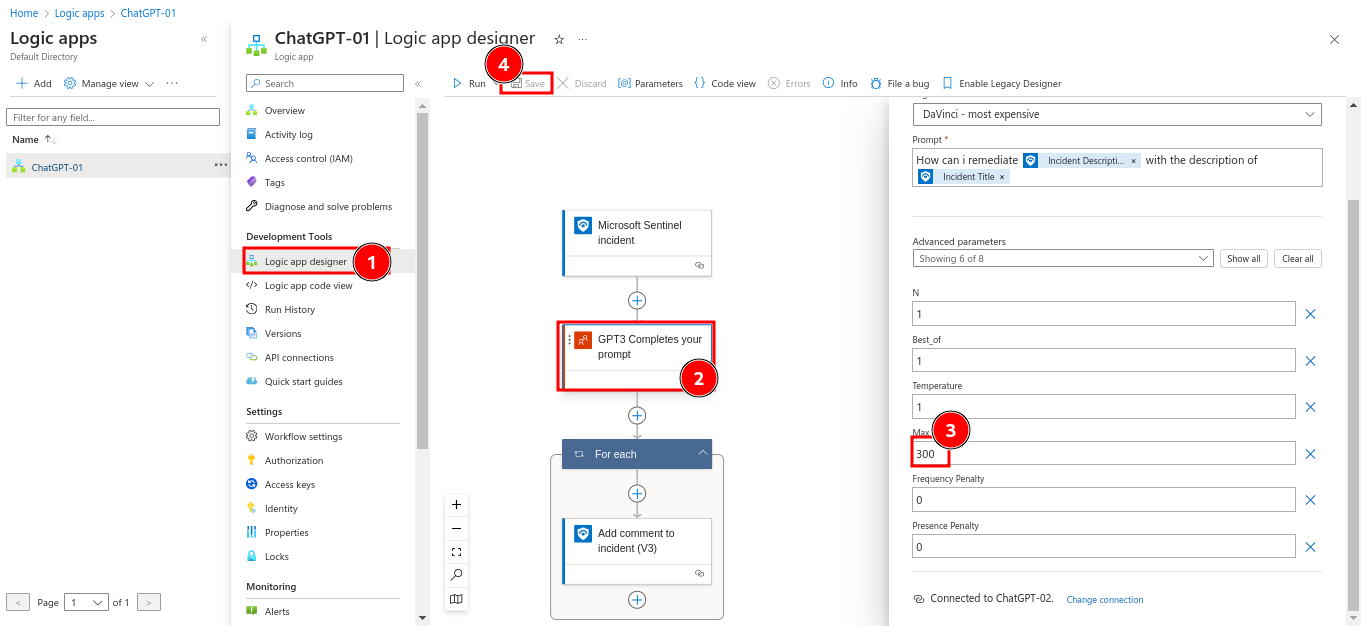
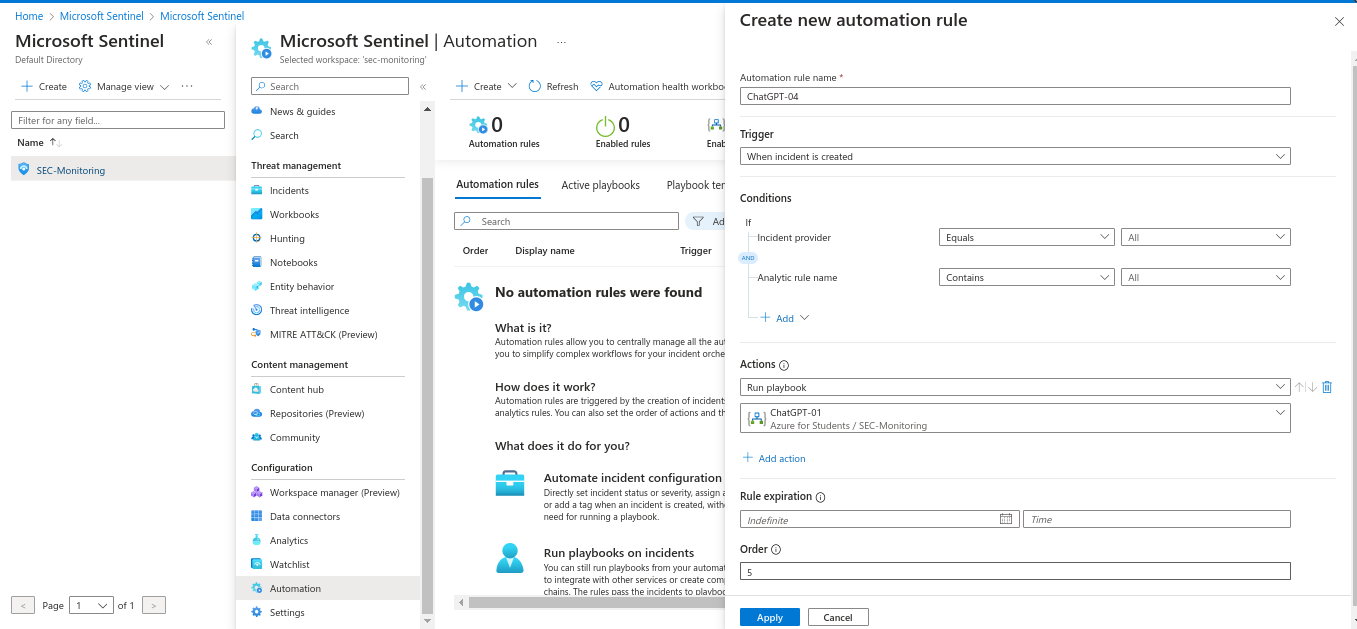
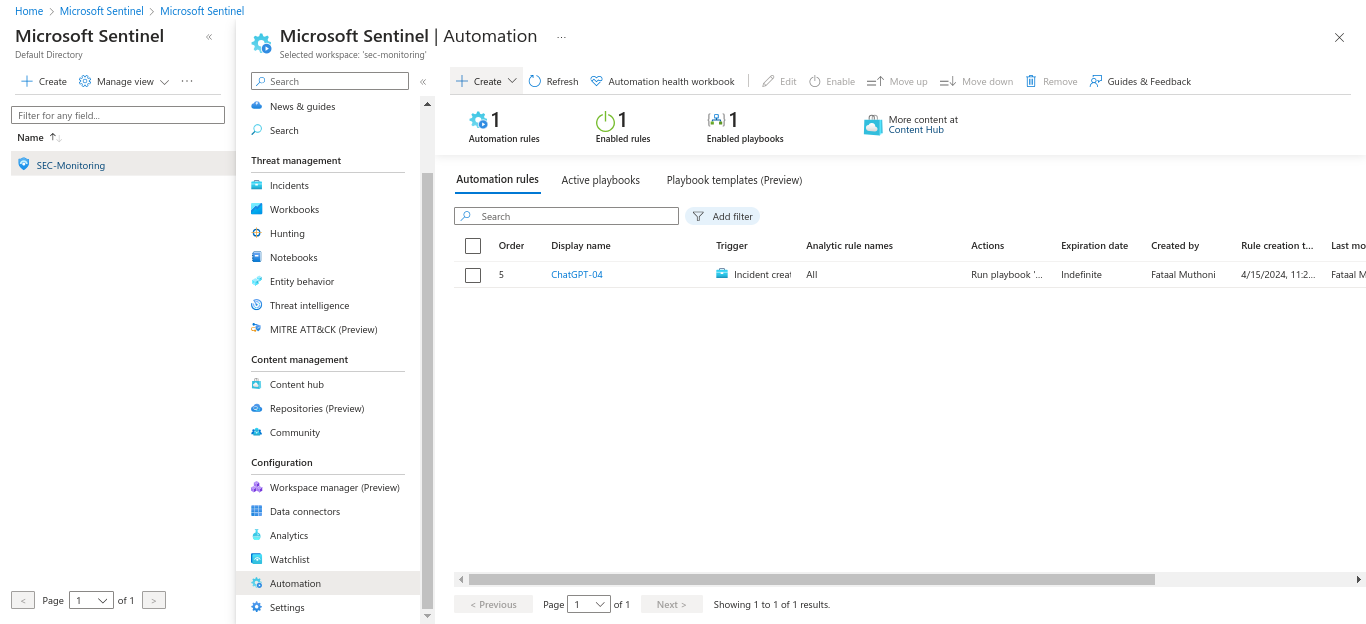
Step 4: Create automation in SIEM with ChatGPT
I created automated workflows to enhance and streamline incident response processes by setting up an automation rule in Sentinel to trigger the ChatGPT playbook for specific incidents.
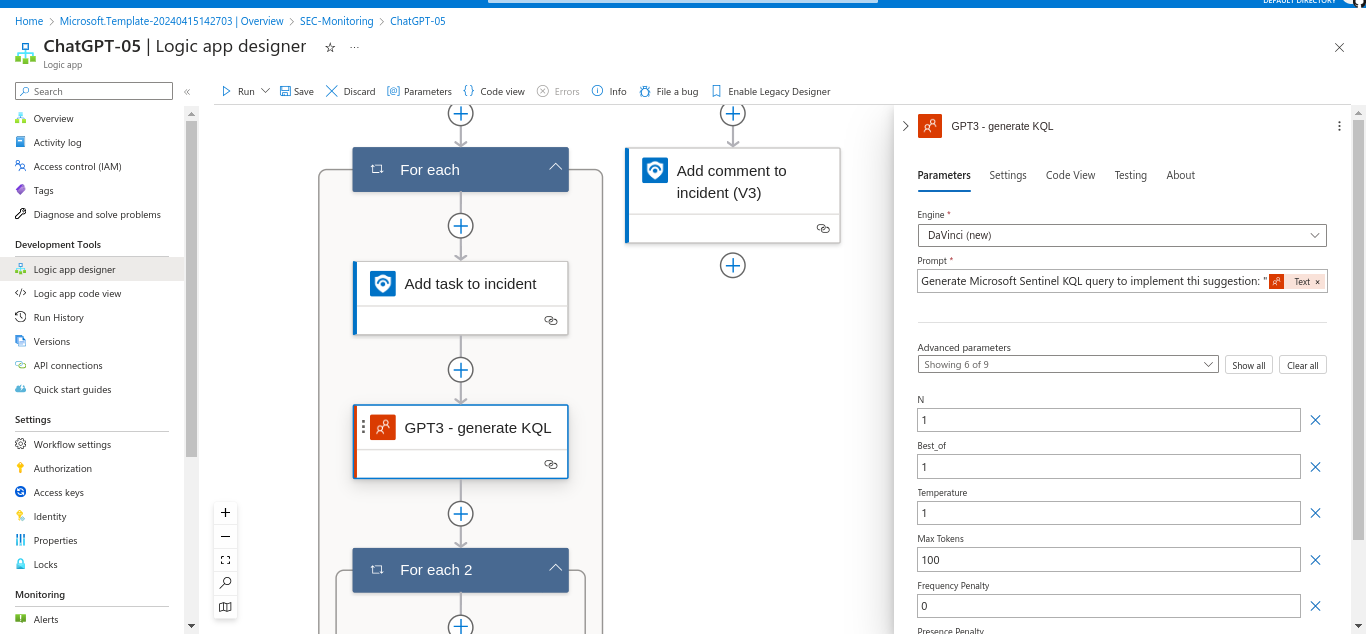
Step 5: Complex integration of AI with SIEM
I navigated the challenges of AI-SIEM integration, ensuring seamless data flow between Sentinel and ChatGPT for advanced analysis.
A flowchart in the Logic App designer, integrating Sentinel logs, ChatGPT analysis, and response actions
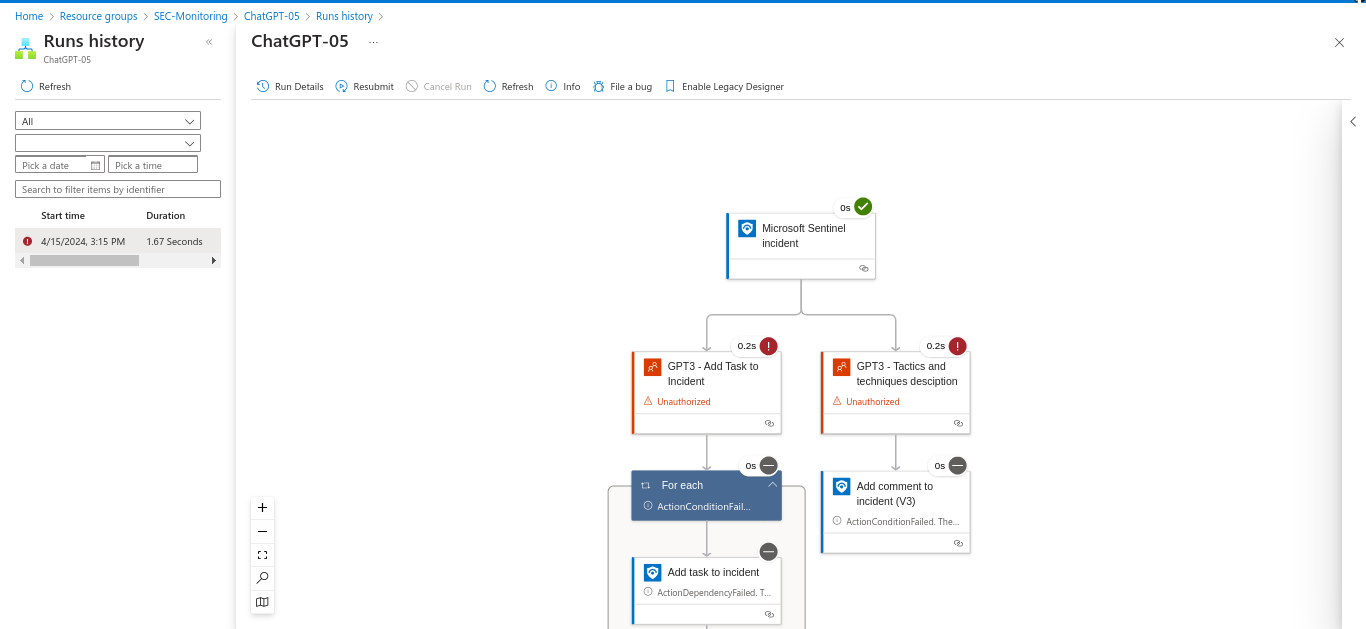
Step 6: Troubleshoot errors by adjusting the playbook
I addressed issues by updating the integration playbook and modifying the connection to align with our current setup. Checking the Logic App logs and adjusting the playbook if errors occur is advisable too.
A failed run with an error message 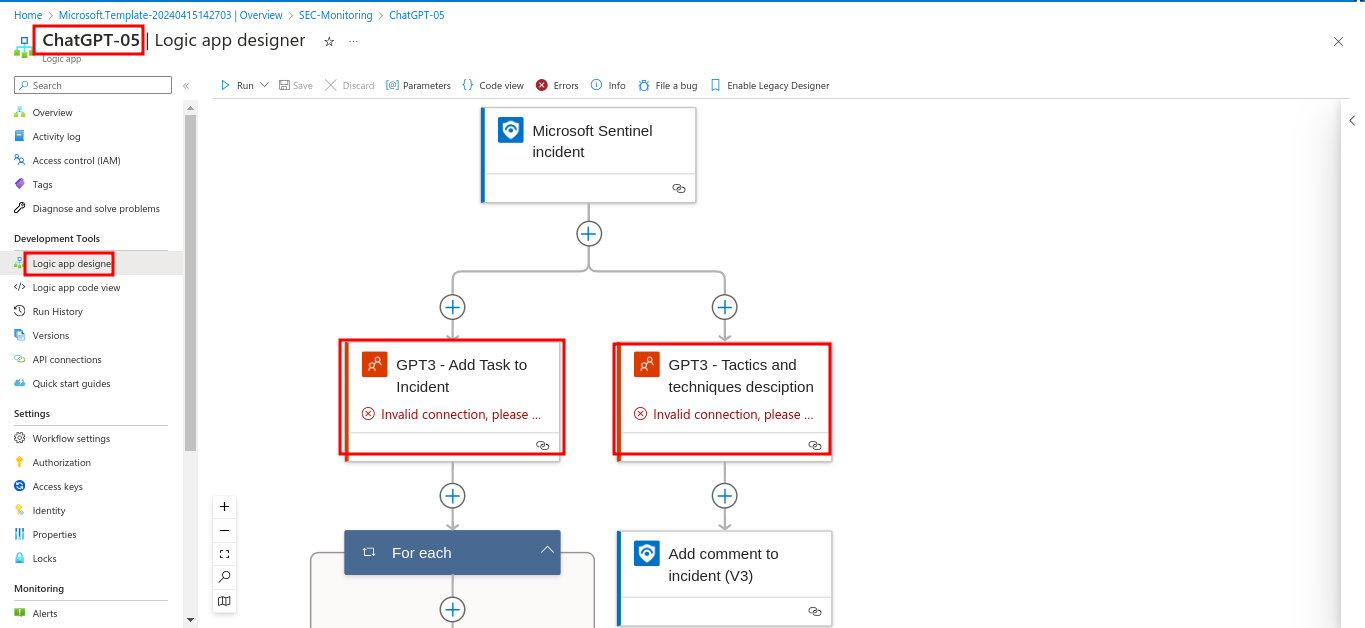
Conclusion
This guide walks you through deploying Microsoft Sentinel on Azure and integrating it with ChatGPT to enhance cybersecurity. By following these steps, you can set up a robust SIEM system, connect it to critical data sources, automate responses, and leverage AI for deeper threat analysis. Regularly monitor and optimize the setup to adapt to new threats and organizational needs.